A few days ago Nomad bridge was hacked and all liquidity drained. You all will also remember the hacking of the Wormhole about 1 year ago. The Wormhole connects the Solana world with the EVM world (Ethereum, Avalanche, Polygon, Bnb Chain, etc). Chainalysis estimated that $2 billion worth of cryptocurrency was stolen from cross-chain bridges through 13 hacks this year - nearly 70% of the total crypto stolen. Cross chain bridges try to solve the problem of interoperability between different blockchains. A cross-chain bridge is a protocol that allows a user to transfer resources from one blockchain to another. Users typically interact with cross-chain bridges by blocking funds in the bridge contract. The user is given equivalent tokens of an asset: Usdc becomes madUsdc or Eth becomes wEth. Bridges are an interesting target because they often have a central storage point for funds, which are then "wrapped" on the receiving blockchain. Regardless of how those funds are stored, that point becomes a target for criminals.
THE ATTACK ON NOMAD BRIDGE
Nomad is a very important cross chain bridge known above all because it allows you to transfer liquidity from the Ethereum world to Evmos (therefore the Cosmos ecosystem). It also supports Moonbeam. Within hours, $ 190 million was gone (about $ 1700 was left). When the Nomad bug spread on the Web and Telegram, it seems that it was a copy / paste of the original transaction so the attack spread (only your address had to be changed to receive the funds!). Initially wBtc and later wEth were drained: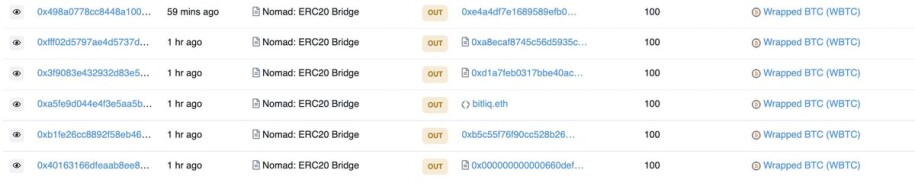
The smart contract made it possible to withdraw funds, without any "guarantee": without depositing anything. 10,000 were stolen in one transaction! Indeed, Nomad's audit had already highlighted this vulnerability, as the `process ()` function, found in the current implementation agreement at Contract (Etherscan), checks that the messages contain an acceptable merkle root. This is intended to prevent users from transmitting arbitrary data.
Due to an error, the team accidentally marked the acceptable root with a zero (0x00) (when using the `initialize ()` function 41 days ago, tx hash ht0x53fd92771d2084a9bf39a6477015ef53b7f116c79d98a21be723d06d79024cad ).
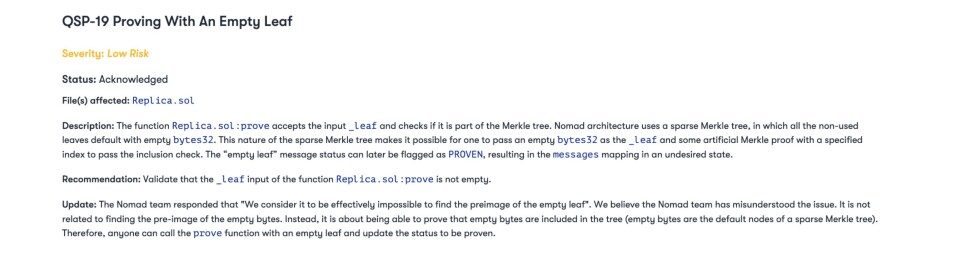
This means that every message is automatically verified by default, which is the opposite of what they should have done. This feature resulted in proving the validity of each message by default.
The result is that on Moonbeam, the Usdc version of Nomad has lost the peg. The other layer1 where problems occurred was EVMos as the native token presented arbitrage opportunities because users rushed to sell all the madUsdc for EVMos (most of the native Usdc blocked in the Nomad contract were stolen). Initially EVMos had a price of about 1.50 dollars on Osmosis (which uses another bridge version of Usdc, that is Axelar) and a price of 5.80 dollars on other dex of EVMos that used the bridged version of Nomad (madUsdc) such as EvmoSwap and Diffusion Finance. The next day EVMos was brought back with a value of nearly $ 10.
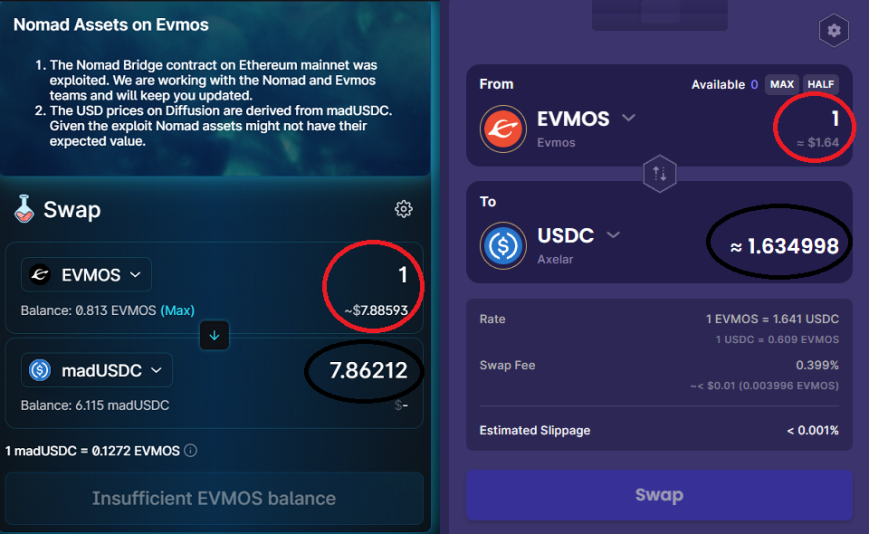
Clearly it is possible to buy EVMos on Osmosis (via Keplr) and then transfer these funds to an EVM (Metamask) address via IBC (Diffusion Finance only supports Metamask). Actually 1 EVMos present on Osmosis 1.55 dollars would be sold at a much higher price (traded for madUsdc). The problem, however, is the liquidity out of Diffusion since there are no more Usdc (guarantee) on the Nomad bridge so if someone does not repay the bridge (as was done for Wormhole) it is an arbitrage operation that makes no sense. Indeed, it exposes to high risks if the price of EVMos continues to rise because madUsdc should be sold in exchange for EVMos (at a loss). Clearly if the price of EVMos on Diffusion or EvmoSwap drops, it would be possible to exchange purchased madUsdc for EVMos (and then sell them on Osmosis).
Regarding the attack, someone was a "White Hat Hacker" and has already reiterated that they will return the stolen funds. This story has shown that cross chain protocols are very attractive targets for hackers. These protocols connect many blockchains so there are many points of attack. They could also suffer from 51% attacks. I remember that on a native blockchain no one can stop you from selling a token. A 51% attack cannot steal your crypto or reset its value! The "wrapped" versions deriving from bridges are simply derivatives: if the "native" funds are stolen from the bridge... the "wrapped" no longer have any value!
Are you interested in ways to earn crypto bonus? Check it out here: Some Sites To Earn Crypto Bonus: Old & New (July 2022)






![How Fear of Piracy [Destroyed] a 20-Year Tech Lead](https://cdn.publish0x.com/prod/fs/cachedimages/3731945950-5c99dbb082c081853735e98f1f9444ea30dc5a195fc83eee84721476c11215db.jpg)



