ICP the Big Indian money play is surging on the crypto markets, which is DFINITY also known as the Internet Computer
All good, except like most ALL Crypto and Fin-tech innovations, the implementation success of these financial settlement solutions is in the operational node network deployment details.
To be clear, this post is not a 'bash DFINITY' post.
In fact ICP 'Internet Computer Protocol' underpinning the Dfinity offer has some real merits. For instance ICP nicely leverages the hierarchical organization of the existing Internet Protocol "IP" infrastructure Internet address topology, and address scheme which connects together this planet's various global, national and regional WAN, Metro and City/town MAN and Enterprise and Personal LAN communication capabilities, allowing the path routing and connection of most Application Network data flows these days.
That said how safe/secure is our Internet infrastructure?
and,
How Safe is Dfinity in that context?
A good question to ask of Dfinity, being they are promoted as being more savvy at IP and would be expected to go beyond the normal configuration of the Internet, would be: What has Dfinity done to fix the OBVIOUS and GLARING known big Internet security holes, like Route Poisoning described in the below Zoom fiasco?
We all know by now about the North American Zoom traffic being re-routed to China, how did that happen?
To understand China's role in Zoom specific development terms read this. (It will give you the 'willies' I am sure)
Dfinity also known as the Internet Computer is surging up the MarketCap charts, and is for sure, as big Whale order router owners play this crypto, the latest 'shiny and bright' casino speculation table. They give good Marketing Spin I will give them that, matching and even exceeding #Cardano in this category, achieved largely via a much more engaging CEO UK front end.
So as a result, my red flags were raised, I did a bit of a 'tech dig' to analyse and better understand ICP in the context of security to see if they did indeed add any investor value in this regard.
What jumped out at me right away, not surprisingly, is the complete and utter dependency of Dfinity as an "Overlay' Application Network' on the Internet as it's deployed, security holes and all, and Dfinity's 'blind trust' of the Internet to be secure, with really no mention I could easily find (still looking) on how to SAFELY deploy ICP and Dfinity as a potential node operator.
One search of the 'bgp' string on Dfinity's development forum https://forum.dfinity.org/ yielded, you guessed it "crickets, zilch' zero mention.
Let's face it, the Internet's use of aging BGPsec Border Gateway Protocol, which uses a simple PKI handshake to establish trust to adjacent BGPsec routers operating generally as Exterior Gateway Protocol "EGP" Routers, is prone to Route Poisoning and Dataflow hijacking for later hack and crack stealing of data, $$ and your next move, just like all other crypto and FIAT fintech dist. networks.
As investors in crypto, imo one should at least understand the Zoom Hack a bit better to better manage risk by reducing the chance of asset or hard store of value theft as much as possible.
Ok, let's dive into this SECURITY rabbit hole a bit deeper, to learn generally a little bit more about how to avoid Route Poisoning and avoid the hijack of over cryptocurrency settlement dataflows to nodes unknown used to copy and store the data-flows, an later, do the Hack and Crack on those flows with Super Computers to steal funds, trade secrets the latter used with conversational info stolen to have nefarious crooks predicts our every move in business, finance and tech, which helps them, put you, out of business faster. Not nice.
The only known way at the moment, I know of, to stop route poisoning is through secure data-flow isolation, a technique which is now commercially available and professionally supported as open source by Anapaya of Switzerland, so any crypto node or network operator can acquire their solution to plug this BIG security hole, ie- stop ZOOM re-routing of traffic to China example state above, where the traffic flows get copied and Super Computer Hacked and Cracked..,
So deploying Anaypaya in their terms means 'GEOgraphic Fencing' , that is GEOFence your node dataflows node to node as subscriber selected and routed dataflows, using SCION exterior gateway protocols and routers (Anapaya SCION software router and beacon instances containerized and running on MetalaaS is likely the quick fix mounted in front of your local LAN connected to the greater Anapays managed WAN service network.).
More on Anapaya here, More on SCION here
On closer inspection of the Dfinity website, forum and related documents, ICP Dfinity, not surprisingly, like most all other crypto players, don't really discuss or even raise the question of the BGPSEC omnipresent threat to their dataflows.
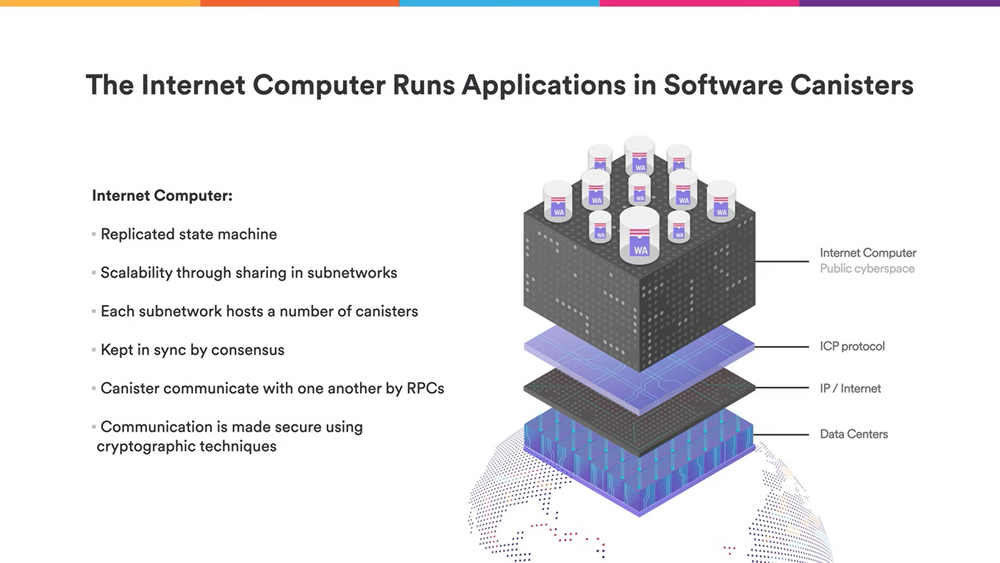
That said, the Dfinity solution is so Internet Protocol, Subnet centric right up to their upper layer canisters model , you would think #Dfinity would talk a little more about good deployment practices, non? :)
Meaning Dfinity like all other crypto plays should have it somewhere in their documentation that the Internet BGPsec Protocol is badly broken AND very susceptible to Adjacent route poisoning from an Adjacent Router's down stream route tables, that is when your BGPsec router gets busy, it trusts any adjacent router after their PKI public/private key exchange (validated handshake) and that is it... That BGPsec router has no way of knowing which downstream BGPsec routers the Adjacent router has trusted downstream...
But and here is the crunch dataflow routing/switching use case which causes all the problems, your BGPsec router gets busy it redirects and sends overflow dataflow streams, in the example above, your Zoom Stream, to the adjacent router anyway, cuz it's trusted..
Meaning any one in the alternate route downstream handles your dataflow which , in the case above ended up in China, for copying, storage, and later Hack and Crack Analysis to listen in and or steal any info discovered in that dataflow...
Which means ICP and Dfinity is fundamentally broken, UNLESS you switch your ICP Dfinity Deployment to be protected as a Private TCP/IP WAN using SCION which is open source, and Anapaya at the moment to get commercial support, as this is the only commercial spin out company of the SCION effort at ETH in Zurich, Switzerland which can stop this "Route Poisoning" from happening which triggers the copying and later theft on infor from your dataflows, unbeknown to you because your traffic does your dataflow does arrive, seemingly without a hiccup . SCION and Anapaya stop all this by letting you, via their Console Connect User Interface and technology service partner (also based in HK with deep CN/CCP money pocket sources), select your service provider Intenet Protocol layer 3 paths, one segment at a time for each route.
So while ICP Dfinity shows great promise, actual operational success of ICP is in the implementation details for each operator of ICP Dfinity nodes.
Get it wrong by using just BGPsec and well, that mistake puts you as the crypto node operator and the whole Dfinity ICP Network at risk of data and $$$ theft, which puts you as the operator of ICP Dfinity Node in a situation where you could be sued into the ground.
In fact Dfinity ICP is not alone in thinking the Internet just works and is secure.
MOST ALL crypto node networks are reliant 100% on Internet Protocol and BGPSec exterior gateway routing have the same exposure, with copying, store Hack and Crack going on right now in real time.
Same goes for the FIAT world of Fintech!
So stopping the dataflow hijacking with SCION or anything you can find similar is a big opportunity for ALL crypto plays of all types to clean up their security act and start providing decent advice in their documentation to their prospective node operators about how to deploy their nodes securely as a mesh High Availability network over what is an anything but secure worldwide Internet.
Conversely, imo to de-risk investments in crypto, crypto investors and traders alike need to start paying MORE attention to security over the Internet and go with the crypto node mesh players that really understand security over the Internet, and start demanding their favourite crypto players clean up their node deployment acts.
TK over and out..






![How Fear of Piracy [Destroyed] a 20-Year Tech Lead](https://cdn.publish0x.com/prod/fs/cachedimages/3731945950-5c99dbb082c081853735e98f1f9444ea30dc5a195fc83eee84721476c11215db.jpg)



