We have uploaded the Nexus Development & Ambassador quarterly report for July 2020 to Publish0x in order to make available information on past development updates.
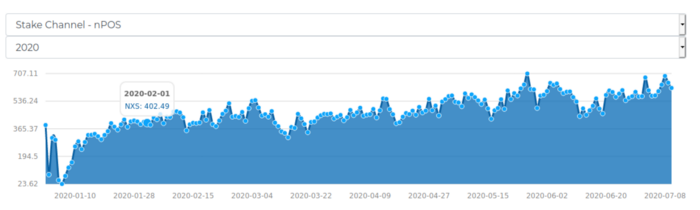
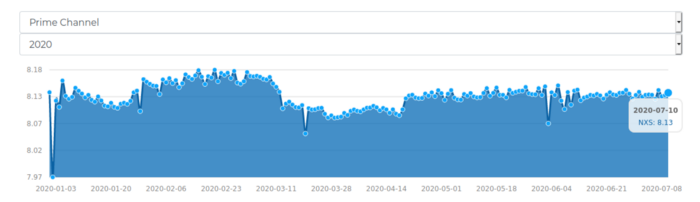
Current Blockchain Metrics
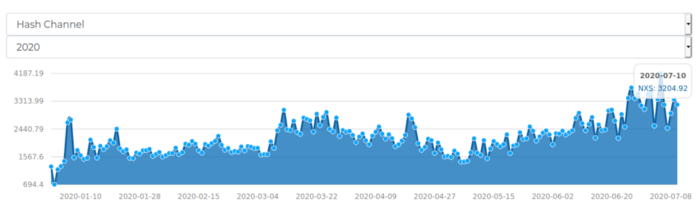
The below graphics are pulled from the Nexus Blockchain Explorer Metrics section showing mining difficulty statistics on the blockchain for this year. Please visit the Nexus Blockchain Explorer and NXS Orbital Scan website for updated and additional blockchain information.
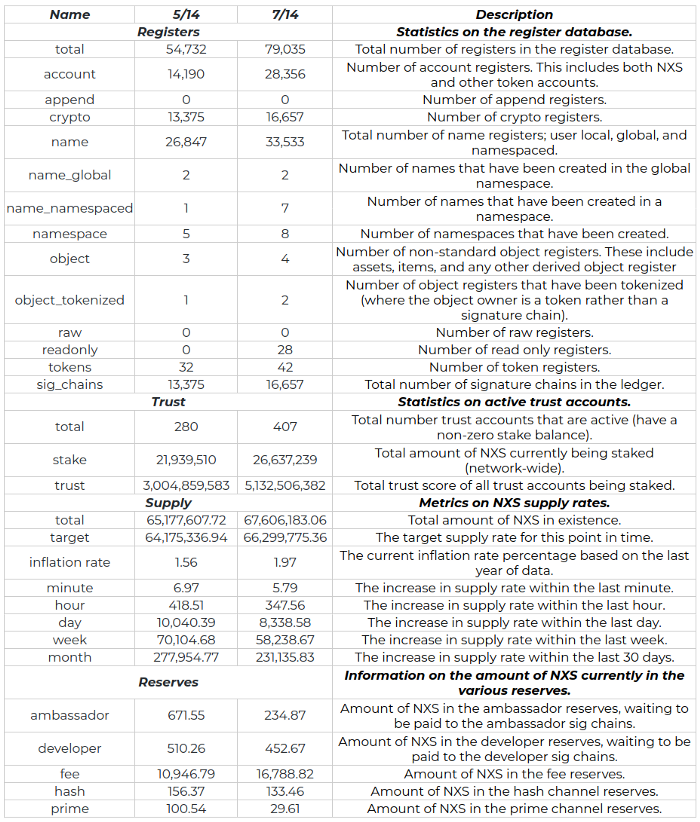
Examining the number of tokens, accounts, names and similar values can provide greater insight into the development activity on a blockchain. Between Q1 and Q2, the number of account registers on the Nexus blockchain have grown 99.8%, while the total Signature Chains (SigChains)gained 24.5%. Additionally, we have seen a 5.8% increase in overall NXS staked vs total supply, increasing from 33.6% (Q1) to 39.4% (Q2). This shows improved engagement in the ecosystem and willingness from users to self manage funds and help secure the network. The below information is pulled from a node using the System Application Programming Interface (API) functions. specifically the “system/get/metrics” command.
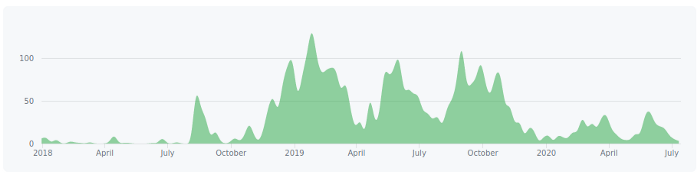
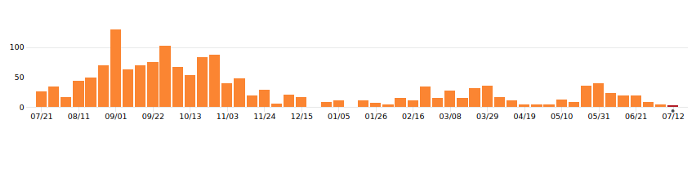
Github can be another great guage for the level of development activity. It is clearly not a timely or ultimate indicator as many tasks, activities and related work are done offline until ready to be merged. This is especially true for Nexus considering extra-curricular activities such as consulting, onboarding and piloting new Dapp projects as well as innovating with satellite, terrestrial mesh networks and other special projects being worked in parallel.
The below charts are pulled from the Nexusoft Github repository on the insights page. LLL-TAO has received the most activity although additional progress on other portions of the project are reflected on the website as well.
LLL-TAO contributions to master
LLL-TAO merge-commits
Development Updates and Accomplishments
05/27/20 — Rice Crypto interviews Colin in a two part series — All Things Nexus Blockchain With Colin Cantrell Part 1 on YouTube and Colin Cantrell Unfiltered CoronaVirus Fireside Part 2 (Patreon Exclusive)
06/15/20 — Colin and Chuck Williams discuss Nexus Safenet, Web3 technology and how Nexus is changing the internet landscape.
06/24/20 — Scott Simon shared the first pooled staking block combining 2 stake transactions (genesis and trust) into a single block on testnet. The trust transaction is the block finder below.
07/07/20 — Nexus Developer Zoom Update — Another amazing update from the development team. A near verbatim transcript is provided below with key highlights in quotes.

Initially, there will be a Decentralized Application (DApp) registration to authenticate and associate user accounts to the DApp. This will simplify the creation process allowing developers to drop in and easily build native DApps with React. It will enable the trustlessness, redundancy and security of a non-custodial solution while supporting standalone or multiple DApps that share the same node.
DApp registration via authentication is the current architecture Nexus is moving forward with, however, it is open to community suggestions. A DApp user will need to log into their SigChain to gain access although additional security precautions are being applied and considered. This is basically a type of sandbox isolation that will progressively be improved.
When a user authenticates to the DApp they will be prompted on the wallet to authorize access. This will eliminate the DApp from handling logon credentials while preventing a wide variety of potential vulnerabilities including DDOS. Banking and other heightened security implementations typically require independent authorization for similar adjustments. Additionally, the dev team is creating a framework to quickly create and iterate DApps.
Because this is not a typical mobile wallet that doesn’t maintain blockchain state, but instead a core node, it is taking much longer to work out the intricacies. Client mode will only maintain blockchain headers and SigChain data so the disk footprint will remain small (approx 240Mb for the current chain height). This type of packaging has not been done before and IOS has been a significant challenge. Huge props to Kendal for driving out all the issues and overcoming the obstacles!! This will change the way users and developers see DApps!
An IOS node is running although we are still working through an Argon2bug, although the path looks clear moving forward. Krysto’s production UI is near completion and the core component Kendall is working on will be merged with this soon. The architecture we are striving for is breaking new ground. Similar solutions have been attempted, for example, a DApp browser for Eth was briefly available on Apple, Google and Coinbase but removed quickly.
Client mode will be released on the next hard fork along with pooled staking and Lower Level Database (LLD) performance enhancements. The client mode will be the first option for all wallet installations, including desktop. This provides a quick sync and minimal impact (approx 20mb of RAM) option applied by default.
Staking will still require a full node, client mode does not have the full blockchain history so establishing trust and preventing double spends will be a challenge. There are a few ideas on how to address this although it will take time to sort out and staking will not be included in the first release. Apple also removes apps with mining functionality, so this is another hurdle to jump.
Notifications Processor
The notifications processor can now be enabled in multiuser mode. The notifications processor is a service that runs in the background managing transactions and wasn’t previously available in multiuser mode. This is necessary for developers running DApp servers with numerous users logging into the same wallet.
Bubble
Bubble is a rapid app development tool similar to Wix, Weebly or other no code web application creators. It has a connector that can snap into the Nexus API. The team initially using this for development decided to leverage their efforts to create a plug-in so this can be downloaded and reused by anyone.
“This will enable easy development for DApps, even for average users without coding experience!! For instance, to create a login screen for a DApp and tie it into a Nexus node literally takes minutes. Then one can create users, tokens, assets or anything that the Nexus API exposes to build any creation of your choice.”
While most of the work on the plug-in has been accomplished there is still documentation and testing being done to finalize. Additional efforts for full instructions including how to setup a Nexus testnet with the plug-in to get folks off the ground quickly is being developed. Once these are complete and fully vetted they will be released to the public.
LISP

Nexus is developing its own implementation of the Location Identifier Separation Protocol (LISP) being written in C++ so it maximizes bare-metal efficiencies that are currently not available in LISP implementations. The team ultimately decided not to utilize lispers.net’s implementation because it only worked on Debian based systems, where full cross platform functionality between Linux, Windoze, and OSX are minimum requirements for components of Nexus. You will see more of this new protocol integrated directly into the nexus architecture, so that your sigchain will provide you routing identification services, sharding, and many more features that were not previously available.
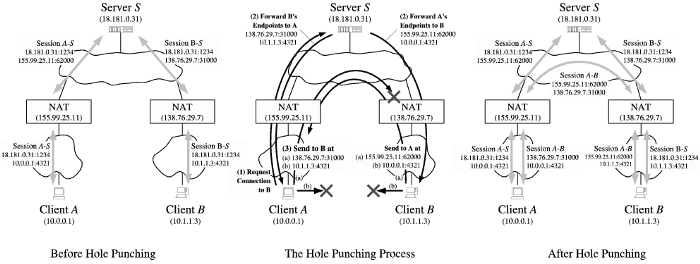
Re-encapsulating Tunnel Router (RTR) is a component of LISP. Development of the RTR is underway and the team is currently working on UDP hole punching. Think of the RTR as a server that has a public IP address, so when you make an outgoing connection it punches a hole through a Network Address Translation (NAT) to establish the connection with a specific port. The connection will not run through the server, it just maintains port and related connection information.
Four different network traversal techniques will eventually be supported: UPNP, NAT-PMP, Port Control Protocol (PCP) and RTR. Eventually 99% of the Nexus nodes will likely be available on the internet through one of these methods, however this will not induce vulnerabilities. In order to keep a traversable hole in the router, keepalive packets need to be constantly initiated from the node. The NAT will act similar to a firewall for the public IP address in that it will drop all connections except for the peer established using the network pipe on a particular port that will close automatically when traffic stops. The NAT does not replace the need for a firewall, it merely provides similar functions in a limited capacity.
This opens the door for so many user experiences with secure application to application (App2App) capabilities. For example, take a simple btc transaction, to obtain the receiving address and send a transaction, this can involve a number of different devices and applications depending on the situation. With App2App secure connections this will remove the complexities involved in device to device communications. The P2P genesis ID association also provides elevated security proving the identity irrefutably when necessary, for example when needed to send large sums of money.
“These sessions are cryptographically authenticated eliminating spoofing and other common problems with the internet. The TAO framework changes the landscape for all types of developers and projects, not just blockchain. An application like Signal could be built on Nexus without even knowing one is using blockchain. The barrier for entry has been lowered significantly decreasing developer cycles, especially with consideration of the Bubble inclusion.”
Paul has begun working on the Filesystem API that will include file metadata as references in blockchain registers. This provides methods to transfer files to each other, prove integrity and more. When Amine becomes available, this filesystem will include new storage mechanisms such as a distributed file system (LLD Filesystem). Another major challenge being overcome with the file system is “gamification” (monetizing hard drive space), as many cryptocurrency implementations using IPFS are currently encountering.
Think of it as a decentralized cloud with incentives to pay your peers rather than to large corporations. The plan is to provide a selective function so if one wants to utilize a known peer for storage this can be achieved. Reputation will be applied to establish additional security and reliable selection bias so even unknown peers will earn trust in the system, and this trust will be directly related to that node’s ROI, creating a direct feedback loop for merit built in the system, and the monetary impact it provides.
Satellites

The Amine distributed file system segways into Satellites. The LLD Filesystem is the first step towards the satellite storage system. The first satellite was purchased back when Nexus was working with Vector Space Systems (VSS). VSS’s GalaticSky was a system virtual machine designed to load software for various solutions like renting storage on a space cloud. However, there were a lot of architectural challenges, such as monetization of services, trustless capabilities and many more. The shortcomings in this collaboration ended up being a blessing in disguise, as the available architecture was constraining and the data management model was limiting to say the least.
When in orbit, it’s important to minimize onboard processing as much as possible. Satellites are moving through giant radiation fields, which are essentially beta particles or electrons. With the way a transistor works, for example a N channel transistor, it uses a higher voltage on the gate to trigger the switch to open. Flying through space with all these electrons floating around, they start collecting in the transistors and the build up can eventually flip the bit causing it to open unintentionally. What should have been a zero now becomes a one, breaking many parts in the system if gone undetected. In order to provide compute effectively, high redundancy and shielding needs to be built into the system.
Typical routers use a stateful system that apply routing tables to direct traffic to a particular location, mapping a hardware address (IP) to a physical location, essentially allowing a computer or physical device to send electrical signals to another physical location, so in essence your IP address contains a known physical location associated with it, which is how packets get from one side of the planet to another side.
One of the critical portions of our design is a stateless routing solution, it does not need to know about anything on the network except the node location and common neighbors. There is no need to update routing tables, exchange information or other cumbersome activities required for managing state. When dealing with the extraneous conditions of satellites, managing the smallest amount of information is crucial.
“The routing system has materialized far beyond what the team expected, significant progress has been made. The possibilities of satellites that seemed distant on the last meeting are now looking to be obtainable in a much shorter time-frame!!”
Routing will not be in a ring network structure but more of a fixed state (e.g. satellite to satellite). For example, if a satellite is accepting packets from another but does not forward, then it will slowly degrade and eventually be removed from the network. This will create the incentive to provide continuous routing services including multicast traffic which ISP only does in a limited and questionable capacity.
Providing a Return on Investment (ROI) to everyday people will ensure that a decentralized Satellite network will be built and maintained, just as the Nexus blockchain has. The benefits need to be something users and organizations can monetize. Therefore, the value proposition of building our own decentralized satellite network is very high for many reasons. The unit is physically isolated by an atmospheric margin significantly diminishing the ability for side channel attacks, physical theft or similar. Furthermore, satellites and the intercontinental routing system provide additional layers of redundancy for the many earthly disasters that could take shape. Given the elevated security and contingency stature of the environment, the price per byte of storage will be at a premium in comparison to ground based options running the LLD Filesystem.
One example of a continuous disparity is Internet Service Providers (ISP), the internet should be free to consumers, and only monetize service providers (e.g. websites), without censorship or surveillance.
Internet Censorship and Surveillance 2018
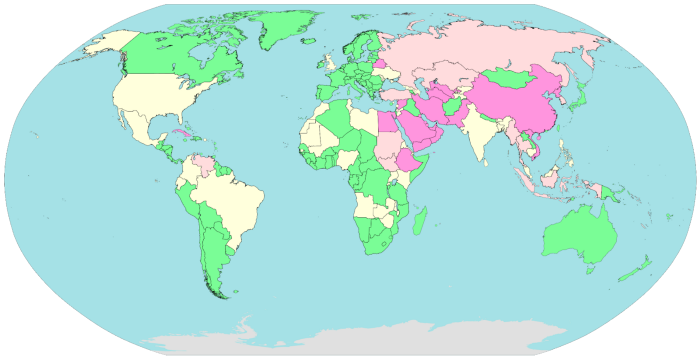
The majority of the hurdles in the design of the satellite network have been overcome. The major obstacles were frequency licensing, value propositions, gamification, technical architecture, physical hardware and routing. Routing was crucial because the IP (Internet Protocol), BGP (Border Gateway Protocol), and others would simply not fulfill our long list of requirements.
07/20/20 — Rex Bear from the Leak Project provides an amazing interview: Quantum Internet & The Biggest Shift In History: Nexus, This Changes Everything, Colin Cantrell
- The conversation begins with Colin’s history with programming, rockets and economics as well as creative minds, concepts and projects that have inspired his evolution into the creation of Nexus Three Dimensional Chain (3DC).
- They progress into problems with societies, economies, and the internet we use today, and how truly decentralized blockchains enable solutions to solve these challenges.
- The discussion spins into the new Nexus operating system being designed and philosophical constructs, game theory, incentives and related topics. They also cover Safenet innovations including stateless routing, decentralized satellites, mesh networks and more. Overall, this is another magnificent, must see interview with Colin in top form!
Community Updates and Accomplishments
05/20/20 — Ahmed Asaad (Medo), posted an idea on Telegram regarding an inheritance module for distributing funds to a desired address, either evenly or weighted, based on preset conditions (e.g. Owner hasn’t logged into their SigChain for 12 months). This would basically create a “Will” or dead-man’s switch function for Nexus and token holders. The development team has added this on their list of features to work on. Great concept Ahmed!
05/25/20 — A sleek new block explorer was created for the Nexus website. Great job, Glenn Bogaerts!!
05/25/20 — An incredibly thorough article was provided by BitShills titled, “Nexus — The Most Advanced Universal Blockchain”
05/29/20 — An excellent article was published by a community member highlighting the benefits of Nexus and why destination moon is soon!
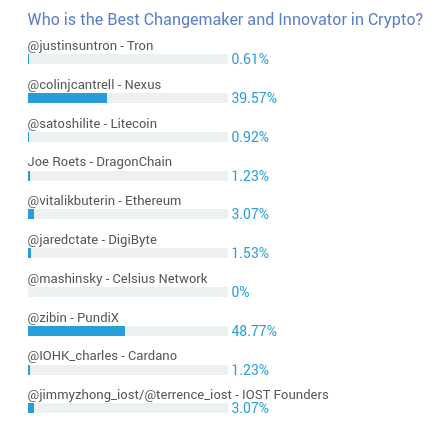
05/30/20 — Colin Cantrell nominated for Uptrennd.com poll — “Who is the Best Changemaker and Innovator in Crypto”. While he didn’t win, second place is certainly commendable considering the competition.
06/02/20 — Nexus Community held a contest on Twitter celebrating the 3,333,333 block mined. 33 NXS were awarded to the first person who posted the appropriate answer in our Official Telegram. We decided to honor two winners, @kanchapun2 and @Redrose27759695, who both posted at the same time. Congratulations!!
06/10/20 — Invoice DApp Module overview was posted to the Nexus website.
06/14/20 — Community members tweeted a challenge to the cryptoverse.

06/16/20 — Nexus Blockfolio has been updated. Huge kudos to Ahmed Asaad!
06/18/20 — @TheLibertyADVSR and @colinjcantrell discuss the Pentagon’s plans to counter a $BTC uprising, panoptic perspectives into historic & current agendas shaping conscribed narratives, consciousness & how #NXS is positioned for resistance
06/19/20 — A Linux Nexus wallet installation video provided by Aeonwise (Telegram Name).
06/29/20 — Nexus Decentralized Identity published on Medium.
07/15/20 — SmileyGnome was interviewed by Shepard Ambellas show titled Covid and Crypto. Topics covered in the interview with SmileyGnome highlighted Bitcoin, Nexus, blockchain, decentralized/distributed software and hardware technologies, and Bitcoin ATMs.
07/20/20 — The TAO: A New Framework to Power the Web, has been published on Medium
Partnership, Special Project, Exchange and DApp (Modules) Update
Satellite and mesh network updates were provided in the 07/07/20 developer Zoom meeting. No exchange or partnership changes occurred during this quarter.
06/10/20 — Free and Equal Elections Foundation provides a United We Stand live interview session with Christina Tobin, Chuck Williams and Colin Cantrell discussing topics surrounding United States elections and updates on Nexus DApp progress
- April Bunje put together a shorter video synopsis (15 min.) highlighting the primary conversations. Thank you, April (Telegram ID — Maid)!
- The DApp will provide transparent information about ALL their candidate choices by allowing users to view candidate details, ballot access requirements, interactive candidate support tools, and educational videos.
07/12/20 — The CoolADE project architecture design and requirements refactoring are making great strides!
Roadmap and Roadblocks
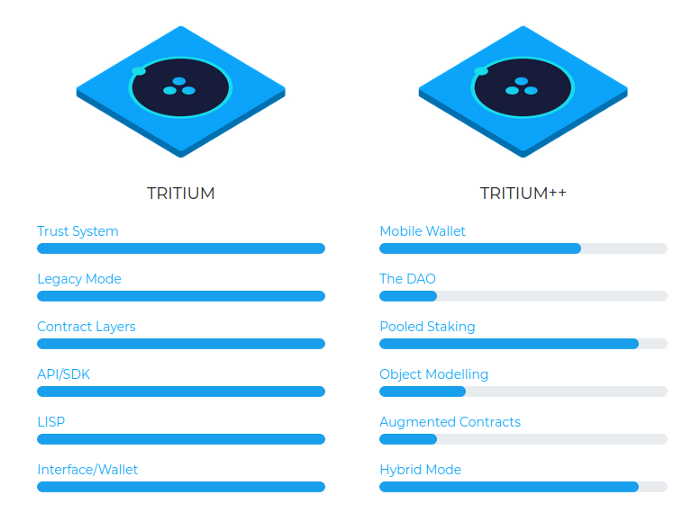
The roadmap below is referenced from the Nexus website.

No roadblocks are worth noting at this time.
Goals for Next Quarter
Pooled staking, API enhancements, performance and LLD optimizations, and mobile wallet / client mode continue to remain top priorities.