Using Stellar's consensus algorithm, PI Network guarantees the ability to "undermine" tokens, directly from a mobile phone, without engaging the CPU of the phone itself, much less the graphic unit.
Let's see how it works.
Before going into the functioning of the PI Network protocol, let's try to understand how the Stellar Lumens algorithm works, albeit in broad terms.
In order to obtain consent, therefore the authorization to validate the block, a node must communicate its solution to all others; through the problem of the Byzantine Generals, we have the almost mathematical certainty that the solution is the correct one: the number of nodes is high and the reward makes the nodes to communicate the real solution they found, without deceit.
This is the validation algorithm of most Blockchains, first of all that of Bitcoin and Ethereum (although ETH is proceeding with the Switch from PoW to PoS); which, as we know, implies a very large expenditure of electrical energy to be able to operate the ASIC batteries used to solve the calculations.
Stellar Lumens had an intuition: instead of communicating to all nodes including the fraudulent ones, let’s setup a quorum (minimum number of nodes to have the consent); may the communication to the reliable nodes be enough?
In this way I greatly streamline the validations, in fact the transactions on Stellar are resolved in 2-5 seconds. Clearly, to avoid in all ways that there may be nodes affected by "Byzantine failure" greater than 1/3 of the total nodes, the nodes selected for validation must contribute to the validation of other transactions with different nodes.
The concept of intersected quorums is introduced.
This type of consent takes the name of FBA (Federated Byzantine Agreements) originating the personal protocol of consent of Stellar: SCP (Stellar Consensus Protocol)
In practice, indirectly, the reliability of the nodes is confirmed, only when there is the intersection of the quorum.
It is clear that if the quorum does not overlap, it takes the name of disjoint and it is not possible to have the consent to validate the block.
The validation process has a cost, albeit small compared to credit institutions, this cost is the reward that the node that has proposed the solution is withheld. This process is known as mining.
This type of validation does not require extremely complex calculations, on the contrary it is based only on network communications between the nodes; this is why PI Network has been able to bring mining to Smartphne by modifying the protocol.
The procedure is simple: as soon as the application is started and declared not to be a bot, you enter the heart of the PI Network.
Access to various classifications, depending on what we authorize to do:
- Pioneer: basic level where only PI token transfer transactions can be performed;
- Contributor: An app user. mobile that contributes by providing a list of pioneers he knows and trusts. This builds a global trust chart;
- Ambassador: An App user who is introducing others to the PI network;
- Node: this is the maximum “charge” that can be had, where all the operations of the previous figures can be performed. This is not possible using only the app, but you also need a special software for a PC or laptop in which you need to run the SCP (Stellar Consensus Protocol).
Considerations:
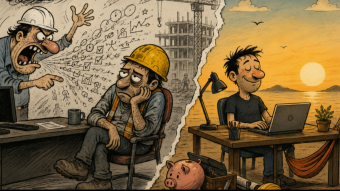
The project in itself is very attractive because, as a pioneer, you only need to open the application once a day to be able to obtain rewards in PI tokens; in all ways, perplexities arise.
First of all is this: are we sure that once the application is finished all the activated processes are closed? If it is necessary to make sure that the various nodes communicate with each other through the network, what better opportunity to take advantage of the radio part of your smartphone?
Once my smartphone is in deep sleep, it may be that the software can bypass google's doze to continue communicating.
From what reported on the WP, the software as a node has not yet been distributed as changes have been proposed to the SCP protocol by PI Netework that will have to be validated by Stellar.
Another drawback of the whole project is that, at the moment, the PI token cannot be exchanged on any exchange in addition to not being listed.
Given the very low investment, I could recommend trying the application, keeping the consumption of both internet data and the battery well monitored, and, as regards the latter, set a restriction in the Google doze if abnormal consumption is found.
Clearly it will be necessary to do some statistics before installing the application to have a reference on the daily use of the smartphone and then install the app.
After that, proceed to collect data on consumption and mined tokens, to see if there is a correlation: High battery and data consumption = higher number of mined tokens / low battery and data consumption = fewer mined tokens.
If, in any case, anomalous consumptions are found despite the google doze being very restrictive, it means that the application is able to bypass certain settings; at this point I suggest you uninstall it.