
Monero is a community-driven privacy-oriented crypto-hawala that was launched in April 2014. It started off as a Bytecoin fork adopting the CryptoNight hashing algorithm for proof-of-work. Monero is also a practical implementation of the CryptoNote technology (which forms the basis of several other privacy crypto-ledgers) -- an implementation of an obfuscated non-traceable ledger with unlinkable payments. It's proof-of-work is being continually optimized to resist ASIC capture and takes advantages of the strengths of modern CPUs (and computationally inefficient on GPUs, FPGAs and ASICs).
Monero means "coin" in Esperanto (a constructed international auxiliary language), and the name was adopted by the community from the initial BitMonero. Other key features of Monero's untraceable crypto-accunting design include the essential double-spending immunity, chain analysis resistance (where with Bitcoin, optimized path-finding methods can pull the UTXO audit trail from unique origin source to final recipient destination) egalitarian ASIC-resistant PoW and flexibly adaptable system parameters without rigid hard-coded constraints (i.e., dynamically self-regulating block size relative to current demand and accordingly adjusted transaction fees).
Monero implements a set of cryptographic primitives (such as ring signatures) in more sophisticated constructions such as to ensure the complete anonymity and concealment of any relevant information (about transacting parties, amounts transacted and corresponding balances), scrambling it in a way that is impossible to observe from the outside. As a community-driven enterprise Monero is also routinely upgraded and systematically improved in line with its principles and end-goal pursuits, so the system is always reliable, adequately secured and well maintained.
Monero is the most popular among privacy coins and the preferred means for transacting and doing business in the murky waters of the darknet and its black market bazaars (used for sourcing all kinds of illegal goods, but mostly drugs and stolen credit card information). Another intriguing use of Monero is for the purpose of breaking/obfuscating the digital audit trails from other crypto-ledgers in what amounts to a kind of cryptographically concocted money laundry.
The group behind the May 2017 global ransomware incident WannaCry, for instance, proceeded to converted their proceeds afterwards into Monero using cross-chain token swap service ShapeShift. In just the first half of 2018, Monero is said to have been used in 44% of cryptocurrency ransomware attacks and has established itself as the standard digital pipeline for illicit capital flows in modern black market e-commerce.
Brief History and Origins of the Project

Monero builds on the foundation of Bytecoin while being intimately linked to the CryptoNote protocol (first proposed in a paper from 2013). The Bytecoin codebase was found to be clean, sharp and very well put together, suggesting that it had probably been refined through time before being released in public (unlike the first Bitcoin working prototype, for example). As discussions and collaboration continued to ferment on Bitcointalk, a community began to gradually form around Monero.
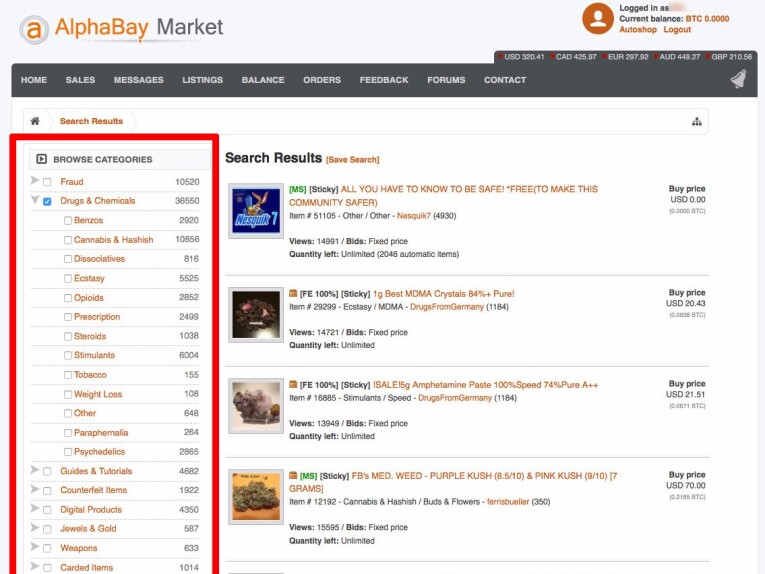
The no longer operational AlphaBay market.
The convoluted arrangements and highly technical cryptographic constructions making up much of the operational components of Monero's transactional crypto engine suggest it has been developed largely by cryptographers rather than software engineers. The XMR currency quickly found its use case applications and dedicated user base in the likes of AlphaBay (most popular darknet marketplace at the time up until the 2017 bust) -- which, after announcing its support for Monero caused the market price of XMR to shoot up to around 6$ (a three-fold increase from the 2$ it was trading at the time).
Cryptographic Primitives and Building-Block Components
Monero does not have hard block size limits, but dynamically adapts (increasing or decreasing) relative to demand and network/transaction fees calibrate themselves accordingly. Although there is a cap at a certain growth threshold to prevent extreme uncontrolled expansion. Below are the cryptographic mechanisms and process-driving algorithms that make up Monero's highly concealed peer-to-peer crypto-system:

Ring Signatures
Ring signatures are a type of digital signature the keys for which are shared and distributed between members of some given group of users that each can perform the signature with his given key, but it is not feasibly possible to determine which one of the group's members keys were used to produce the signature.
Ring signature make sure that transaction outputs are untraceable and provide them with additional plausible deniability.
Ring Confidential Transactions (RingCT)
RingCT is what Monero uses to hide amounts transacted on the network. It was implemented in January 2017, making the attribute obligatory for all transactions on the network after September that same year. It presents an improved variation of ring signatures referred to as "A Multi-layered Linkable Spontaneous Anonymous Group signature", which makes it possible to execute completely hidden transactions (that hide amounts, origins and destinations of transactions) that are reliably efficient and verifiable.
Stealth Addresses: Random One-Time Addresses
Stealth addresses require that the sender creates random one-time addresses for each transaction on behalf of the recipient. Upon creating a Monero account three keys are generated -- a private view key, a private spend key and a public address (public key). The spend key is used to sign/execute payments, the view key is used to display incoming transactions with the destination of one's account and the public key constitutes the receiving address. Both the spend and view keys are used for the generation of one's Monero address and users can decide who they want to allow seeing their balance by sharing their view keys.
Stealth addresses hide receiver destinations.
CryptoNight-Based Proof-of-Work: ASIC-Resistant CPU Mining
CryptoNight is CryptoNote's default proof-of-work hash function. It's a "memory-hard" (i.e., not amenable to ASIC-optimized accelerations) algorithm running on general-purpose CPUs. Monero's active resistance towards ASICs as centralizing technologies that create extreme asymmetries and disproportionate hashrate distribution appears to be a persistent battlefront.
Instead, the Monero community insists on its egalitarian approach to proof-of-work as an essential precondition for non-centralizable censorship-resistance, maintaining a barrier against any centralizing tendencies and forces that might find their way into the network. As such, the nature of Monero's validation engine is one of its most enduring characteristics.
The CryptoNight hash function currently used in Monero's PoW is substantially different from the much more resource hungry and computationally intensive Nakamoto consensus PoW that keeps Bitcoin in motion (at trillions of SHA-256's per second). Monero's PoW also has much smoother rise of difficulty and an approximate block time target of 60 seconds.
The CryptoNight hash function standard is specified and sketched out in a basic text file here and set to be replaced with a more aggressive change (RandomX) with the upcoming protocol upgrade.
RandomX: New Improved PoW Implementation
Monero carries out routine hard-fork upgrades every 6 months and is scheduled for a network protocol upgrade later in October (2019 as of writing). As a deterrence meant to permanently discourage ASICs, Monero introduces some minor tweaks and modifications to the mining algorithm at each such network upgrade (as to render any operating ASICs useless).
The latest upgrade however involves an actual replacement with whole new improved proof-of-work algorithm called RandomX, optimized for general-purpose CPUs and intended to further cement ASIC-resistance in accordance with the Monero community's long-standing principles. The network's continuous routine maintenance and support and keeping the network up-to-date is what ensures a widely decentralized network and a more egalitarian distribution of block rewards.
The way of doing things in Monero demonstrates how security is not a recipe or prescription, but a continuous and ongoing process.
Kovri: I2P Router for Traffic Obfuscation
An independent Monero project for an I2P router in C++ which fires up a hidden TOR-like network (with several technical differences) which, in adversarial circumstances could hide all Monero traffic preventing anybody from knowing it is being used. Kovri is presently in alpha and not fully integrated with Monero. Official project website is found here.
Applications and Use Cases
A peer-to-peer payments engine incorporating such powerful cryptographic techniques and naturally resistant to capture and control, all the while operating under the radar of what could even be detected -- such a technological assemblage has an immediately obvious appeal to the criminal contingents of subterranean black market economies and the whole range of shady and unregulated areas of questionable enterprise.
But Monero's practical applications are, needless to say, not limited to the needs of criminals and stolen credit card peddlers, but provide permissionless open access to an extremely valuable and important public service, especially so in our present day and age of what Shoshana Zuboff has recently described as surveillance capitalism.
Monero provides a means to conceal information which today is all too often used and abused to actively profile us and sell the information on markets that trade in behavioral patterns and human futures or have it fed to decision-making algorithms, invisibly operating in the background of our everyday that manage and manipulate us in turn without our registering it.
Controversies
Perhaps the biggest recent controversy involving Monero has been the discovery of its use in conjunction with cross-chain swap service ShapeShift as the go-to means for transforming illicit profits into "legitimate" assets. ShapeShift was an open web-based service requiring no registrations or KYC/AML forms and Monero was used as the obfuscating point of dissolving any incriminating traces.
The Wall Street Journal covered the story in a short piece titled "How Dirty Money Disappears Into the Black Hole of Cryptocurrency", published in September 2018. The report claims that over $90 million had been laundered on ShapeShift in a single year and Shapeshift itself was forced to introduce registration forms and put a KYC policy in place.
Other Privacy-Oriented P2P Solutions

Privacy-centric crypto-ledgers are a niche category of technologies with an always somewhat ambiguous standing and inconclusive legal and regulatory status. While Monero has established and proven itself the de facto standard for clandestine transfers of funds, Zcash is another popular privacy-enabled Bitcoin fork which makes use of zero-knowledge proof constructions (a particular design called zk-SNARKs) in providing confidential or "shielded" z_transactions.

The cave of Alibaba. Prover is to convince Verifier that he is in possession of the secret word opening the door inside the cave. To do so Prover randomly takes either of the two paths (A or B), while Verifier waits outside. Verifier picks one of the exit paths and Prover reliably appears from it.
Zero-knowledge proofs constitute a form of cryptographic alchemy where a prover can prove to a verifier the validity or truthfulness of a statement without revealing anything about it and on the condition that both the prover and the verifier follow the constraints of the same protocol. The general principle is usually illustrated with the instance of the cave of Alibaba. The Zcash team and its associated academic and research entities are mainly focused on the refinement of ZKP protocols and application-specific constructions. Zcash is essentially identical to the original Bitcoin implementation, except for the ZK-powered functionality of concealed transactions (with optional "selective disclosure").

Perhaps also worth including is Dash, a PoS-modified Bitcoin fork functionally extended with rich features like instant and private transactions. The latter are carried out via an CoinJoin method of attaching transactions together as if to make joint payments, but the value exchanged by each party and the place where the payment ended up are impossible to trace, discover or know by any other third party.
Conclusion and Future Prospects
The new upcoming Monero upgrade will ship with the built-in anonymizing network/router (I2P) for hiding traffic and bypassing firewalls, but the main crucial upgrade will be Monero's new proof-of-work algorithm RandomX which presents a new take on ASIC-resistance and "the strongest effort to-date to prevent ASICs from dominating the Monero network."
Monero is a community-driven enterprise undergoing continuous iterative cycles of development and keeping the system responsive and in check. Also, the Monero community demonstrates a degree of mature sobriety not usually characteristic of the crypto scene at large.
The community-funded first edition of "Mastering Monero" (published in December 2018) is available for download in PDF from here. It's a roughly 200 pages long detailed and easily digestible description of the technology and the principles underlying Monero's design.
-- by @rhyzom (Martin B.)








![[The $0 Growth Hack]: How To Build a 1-Million-User Empire in 2 months](https://cdn.publish0x.com/prod/fs/cachedimages/3731945950-e221973c3b382a1996b83b7ff6d063e191f6be57889a4e0bf3926d37de0a6d35.jpg)

