This hack happened early and was instrumental in shaping the cyber domain.
If you aren’t a medium member, you can read with no paywall via substack
Covering historical hacks and writing them up is pretty interesting. From the early days of the internet right through to the era of AI, cyber investigations and security have evolved and changed, but despite these changes, some things stay the same. For many investigations, the tenacity of the lead investigator plays a vital role in the success of the investigation and can often make or break a case. For today's historical hack, we’re jumping back into the 80s. It’s a world of dialup, timeshare and a basic accounting error that led to a multi-person international espionage ring being uncovered. Let’s get to it!
The Early Days
In the late 1980s, the digital world was still taking infant steps. While this was the start of the era of personal computing that led to the internet, back then computing looked very different. We wrote about time share systems in a previous article, but connectivity was a much simpler thing in those days and very commercialized as well.
 Computers looked different back then. This is an IBM360. Source: Wikipedia
Computers looked different back then. This is an IBM360. Source: Wikipedia
Before we put them in our homes and pockets, in the pre-World Wide Web era, computer networks had become essential tools in research institutions. However, the rudimentary security measures in place made them vulnerable to curious minds and malicious intent. The fact that security measures were much more primitive back then certainly didn't help either. As this new connectivity expanded to bring in defence and government services, so did the potential for unauthorized access. While this was eventually leading to an era where hacking became a serious threat to national security we weren’t quite there yet. By the end of this story though, we were!
The Incident
It was said back in the Cold War days that soviet spies were often identified by little measures that gave away their place of origin. With this in mind, our story begins at the Lawrence Berkeley National Laboratory, where Cliff Stoll was tasked with resolving a seemingly mundane $0.75 accounting discrepancy. Initially chalking this up to a clock error, Stoll expected a quick conclusion along with finding a valid explanation for the error.
Instead, as he started to audit the lab’s computer system, he noticed an anomaly. A user had exploited a single account and was using this account to enumerate the system and then find additional accounts to compromise. If you aren’t the technical type, this means that rather than exploit a single account or machine, this hacker used multiple accounts and insecure systems to eventually exploit machines across the entire United States. If you’re a pentester you probably already know that enumeration pays off.
The Hacker’s Tactics
The hacker at the centre of this was no ordinary intruder. Skillfully exploiting vulnerabilities in the computer networks of various research institutions, this shadowy figure remained elusive, employing tactics that were both sophisticated and shrouded in anonymity. These tactics were also good in evading the tracking systems of the day, with lines needing to be manually monitored and traced through telephone exchanges. This single fact alone added weeks of investigative work to an already complex process.
The hacker’s modus operandi also included exploiting trusted relationships between systems, masking their presence by hopping through numerous accounts and manipulating network vulnerabilities. And, to get his Superuser privileges he’d use an exploit in a program that’s still common today. EMACS.
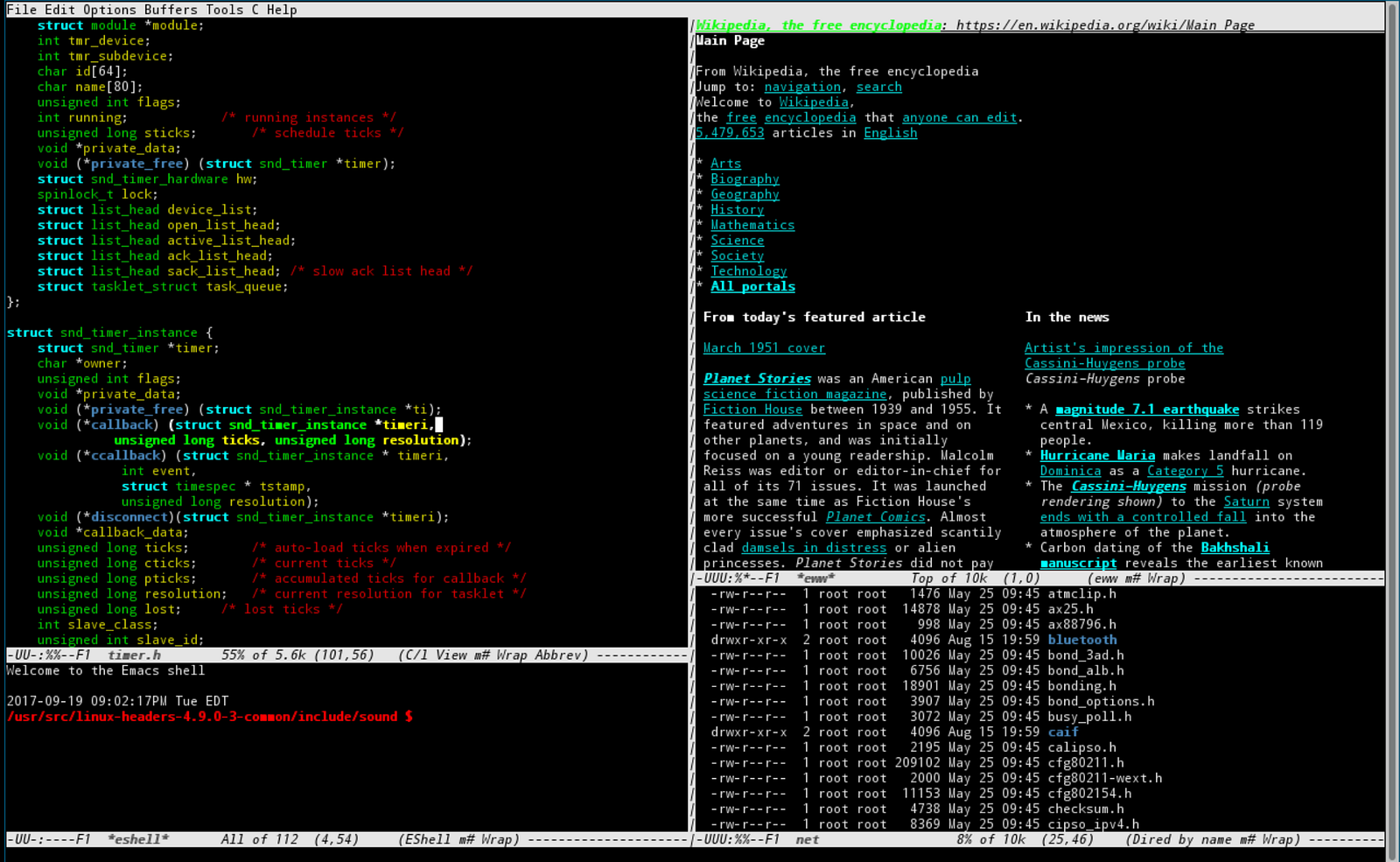 EMACS was exploited to gain superuser privileges. Source: Wikipedia
EMACS was exploited to gain superuser privileges. Source: Wikipedia
While we talked about a lack of cyber response and back practices causing problems in the early days of the internet, the process was even worse back then as many agencies simply didn’t understand the complexity of the problem they were dealing with. Eventually frustrated by the lack of urgency from law enforcement, Stoll took matters into his own hands. With painstaking determination, he began tracing the hacker’s digital footprints, unravelling the web of connections that spanned across the globe and becoming the centrepiece in a multi-agency international investigation.
Stoll meticulously documented every move, using primitive tools when compared to today’s cybersecurity arsenals. This process involved long hours of meticulous log analysis, a keen understanding of network protocols, and a relentless pursuit of truth despite the disinterest of local and federal law enforcement.
There was also a giant stack of 1980s technology. This included a pager, to inform Stoll when the hacker connected to the lab computers, as well as a bank of dot matrix printers that would print and log activities that were performed by the hacker in his terminal during the session.
The Beginning of The End
As Stoll continued his pursuit, the scope of the hacker’s activities became increasingly clearer. The infiltrator wasn’t just a rogue hacker; they were part of a broader network engaged in espionage. The Cuckoo’s Egg led Stoll to discover a connection with West Germany, sparking an international collaboration between U.S. and German authorities.
 The brilliant investigation by Stoll geolocated the hacker to Hanover, West Germany. Source: Wikipedia
The brilliant investigation by Stoll geolocated the hacker to Hanover, West Germany. Source: Wikipedia
In the interest of brevity we won’t go too far into the dynamics of the investigation but what we will say is that some ingenious tactics were used in an attempt to stall and track the hacker. This included touching a key on a hardwire to disrupt data transfer without dropping the line and best of all a completely false disinformation project known as SDI net. This included a large quantity of false data and best of all a mail-in office regarding the project. While the hacker didn’t take Stoll up on this offer, an associate of his did. This enabled authorities to build a picture of the hacker's network of associates and would eventually push them into acting on the issues, leading to coordinated arrests. When these were all said and done, it was West German national Markuss Hess who was identified as the cuckoo. While today, we’d call that strategy a honeypot, in these early days techniques such as these were still finding real-world use cases.
In the final stages of the investigation, it was also revealed that a satellite link was used, as well as the transatlantic connection that we mentioned earlier. As you’d imagine, despite it being early days the hack was still pretty complex as you can tell by some of the listed systems below.
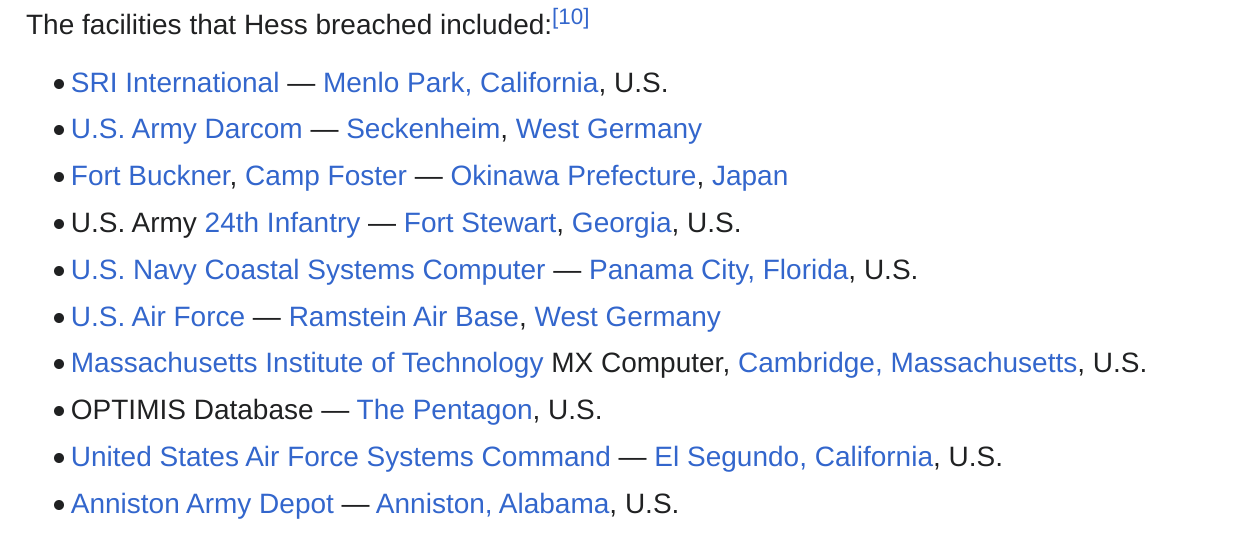
Impact and Legacy
The Cuckoo’s Egg investigation had a distinct impact on the world of cybersecurity. Stoll’s work shed light on the vulnerabilities of computer networks and prompted institutions to reassess and re-harden their digital defences. With Hess eventually being given a suspended sentence of just 20 months, it also began to change the dynamic around cyber espionage and international cooperation around finding and dealing with cybersecurity issues. It also led to new laws regarding computer misuse being implemented in large parts of Western society.
Cliff Stoll’s contribution didn’t end with the investigation either. His book, “The Cuckoo’s Egg,” became a bestseller, reaching a broader audience and inspiring a new generation of cybersecurity professionals. Stoll’s legacy is not only in catching a hacker but in being a pioneer of the field.
Today, Cliff leads a quiet life making Klein bottles in retirement. If this article has interested you, we’d recommend you give his book a read as it’s a great look at both how things work and the analytical mindset that needs to be applied by both cyber investigators and hackers.
Medium has recently made some algorithm changes to improve the discoverability of articles like this one. These changes are designed to ensure that high-quality content reaches a wider audience, and your engagement plays a crucial role in making that happen.
If you found this article insightful, informative, or entertaining, we kindly encourage you to show your support. Clapping for this article not only lets the author know that their work is appreciated but also helps boost its visibility to others who might benefit from it.
🌟 Enjoyed this article? Support our work and join the community! 🌟
💙 Support me on Ko-fi: Investigator515
📢 Join our OSINT Telegram channel for exclusive updates or
📢 Follow our crypto Telegram for the latest giveaways
🐦 Follow us on Twitter and
🟦 We’re now on Bluesky!
🔗 Articles we think you’ll like:
- Software Defined Radio & Radio Hacking Pt 1
- OSINT Investigators Guide to Self Care & Resilience
✉️ Want more content like this? Sign up for email updates







![How Fear of Piracy [Destroyed] a 20-Year Tech Lead](https://cdn.publish0x.com/prod/fs/cachedimages/3731945950-5c99dbb082c081853735e98f1f9444ea30dc5a195fc83eee84721476c11215db.jpg)



