The End of the World’s First Darkweb Market.
If you aren’t a medium member, you can read with no paywall via substack.
Over the last few months, we’ve taken a deep dive into the dark web, by looking at onion routing and the history of tor, while next month we’ll be doing a walk-through for beginners on how to access the dark web safely. In today’s article though, we’ll be exploring the takedown of the Silk Rod marketplace as well as the capture of its administrator. Grab your paranoia, put your feet up and your James Bond hat on. This tale has got cash, encrypted websites, feds and a whole bunch of drugs. Let’s get into it!
What Was The Silk Road?
Formed in 2011, and leveraging several types of new technology including cryptocurrencies and the relatively new Darkweb, The Silk Road was the world’s first online market for illicit goods.
Kind of like an eBay for dealers, Silk Road connected wholesalers with consumers and allowed people to leverage anonymity and the internet in the pursuit of their illicit substances. However, despite the hype you may have heard of, this marketplace wasn’t just for drugs, as all manner of illegal goods and services were about to be sourced through the dark web.
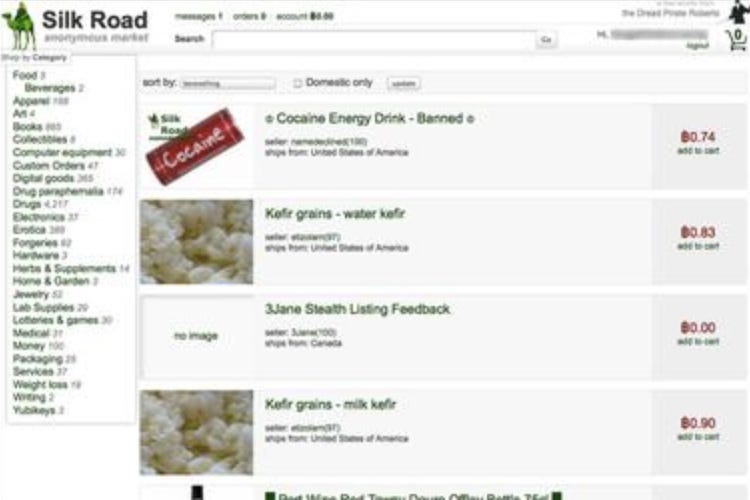
The Silk Road was the world’s first illicit marketplace. Source: Wikipedia.
Growing through word of mouth and initially escaping the eyes of law enforcement agencies worldwide, Silk Road’s popularity exploded rapidly and in the early days promised a safe haven for those wishing to make money while minimising risk. While the website did draw attention, its offshore nature and reliance on automation meant that in these earlier days, it was often pretty difficult to find out who was behind situations such as these.
How Did It Work?
It was in fact, as ingenious as it was simple. Users accessed the platform through the Tor network, ensuring their identities remained hidden. Transactions were then conducted using Bitcoin, our favourite decentralized cryptocurrency that provided a degree of anonymity. Vendors on Silk Road offered a wide array of illicit products, including drugs, hacking tools, and counterfeit items. The marketplace employed an escrow system, where funds were held until the buyer confirmed the receipt of goods. The use of cryptocurrency and the Tor network made it challenging for law enforcement to trace transactions or identify users, contributing to Silk Road’s notoriety.

Bitcoin helped Silk Road travellers stay anonymous.
The website also relied on automation to provide validation services for both sellers and buyers. While this minimized human intervention throughout the process this automation also meant that the process for both buying and selling was exceptionally streamlined. While this helped fast-track the process, it also provided buyers with a layer of protection as verified sellers were more likely to see the transaction through till its closure.
Who’s The Boss?
It was Ross Ulbricht, a Texan with a background in physics and engineering, who embarked on a path that would lead him to infamy as the creator and operator of the Silk Road. Born on March 27, 1984, in Austin, Texas, Ulbricht’s journey took a turn towards the criminal underworld when he founded the Silk Road in 2011. Under the alias “Dread Pirate Roberts,” inspired by a character from The Princess Bride, Ulbricht created an online marketplace on the dark web that gained notoriety for facilitating the trade of illegal goods and services.
Ross Ulbricht created Silk Road and was subsequently jailed for it. He remains incarcerated to this day. Source: Wikipedia.
Ulbricht’s vision for the Silk Road was rooted in libertarian ideals, aiming to create a platform free from government intervention. The site used the Tor network to provide users with anonymity, and transactions were conducted using Bitcoin to ensure a level of financial privacy.
The Silk Road, however, quickly became a hub for criminal activities, including drug trafficking, hacking tools, counterfeit currency, and more. Ulbricht was accused of being directly involved in orchestrating and profiting from these illegal transactions.
On Shaky Ground
As you’d imagine, taking down an international drug empire on a secure network that most people don’t have the knowledge to access comes across as quite the challenge. However, before the first takedown would occur there were already signs that things were not great.
Despite putting in extensive effort building and setting up the verification system bad actors entered the scene causing problems for consumers and retailers alike. In fact, curiously enough it was the anonymity that was causing the problem. Using both Tor and Bitcoin made it harder to verify who they actually were and while this was great for transactions it was terrible for verification.
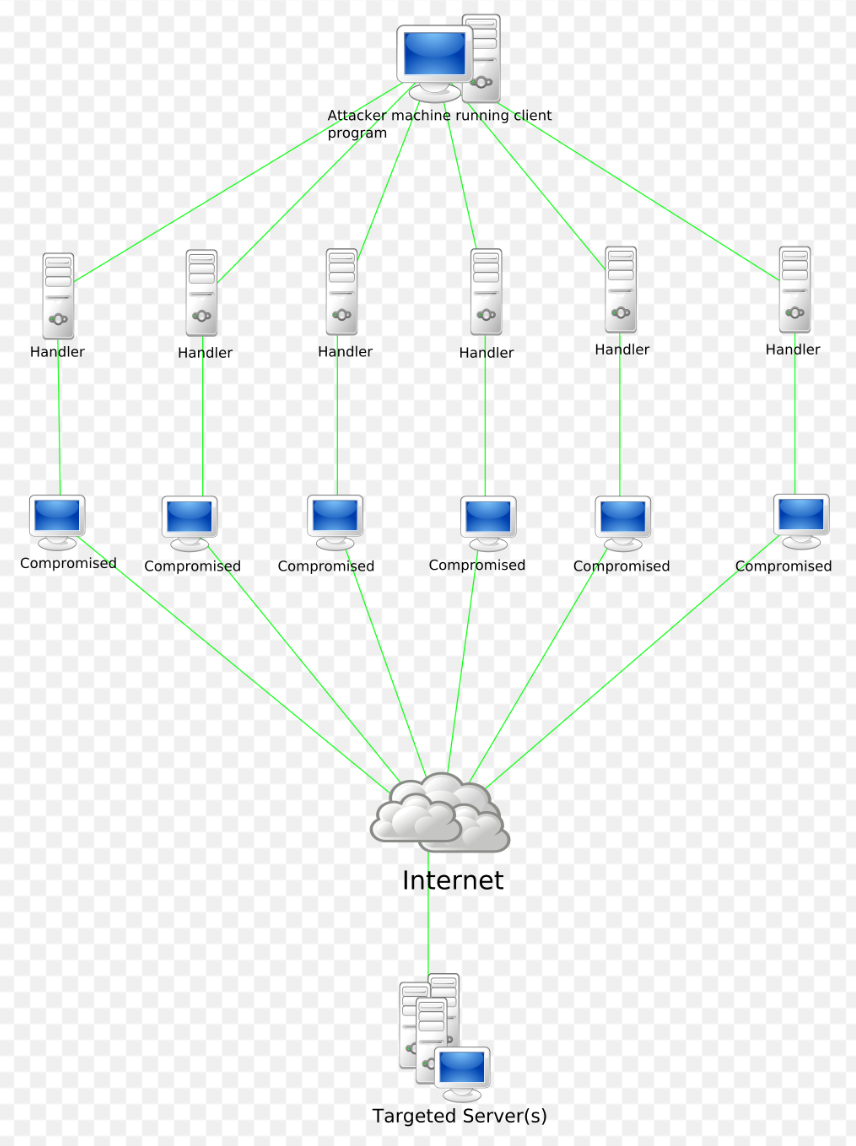
Anatomy of a DDOS attack. Source: Wikipedia
Worse, the whole time this was occurring Silk Road was still being monitored by the long eye of the law with investigators following the money and the transactions able to identify wallets of interest that had been responsible for receiving large numbers of Bitcoin transactions. This created additional problems for Ulbricht as while staying ahead of investigators was theoretically possible, it meant far more work would be required to do so.
Things really came to a head in 2013 though when the Silk Road suffered a significant number of Denial Of Services (DDOS) attacks that brought the website down for some time. Originally thought to be the actions of law enforcement, it came out at the trial that it was allegedly not law enforcement and that other malicious actors had joined in on the party as well. Clearly, at this point, the sharks were circling.
OSINT Go Brr
By the time authorities actually got around to arresting Ulbricht, the stakes were far higher for him than they were at the start. While investigators were looking for Ulbricht using data-matching techniques paired with historical data, a mole had also infiltrated the group and was working from within to unmask the admin. The first steps came when investigators were able to determine Ulbricht’s timezone from his chat logs, however, things really started to heat up when an Icelandic server was seized containing chat logs and other historical data. This server filled in a lot of the blanks for authorities, but it wasn’t quite enough at this point.
The big break would come, and eventually, it would come from the same source that ended up nailing Al Capone. The Internal Revenue Service.

This big break would come from Internal Revenue Services investigator Gary Alford, who was investigating the activities of the Silk Road. Alford was able to identify marketing posts made in the early days of the Silk Road. This wasn’t great for Ulbricht, but where things really came unstuck was when Alford was able to link a programming question back to Dread Pirate Roberts, and it was this question that led to Ulbricht’s eventual arrest. It was a single word that gave the game up. Using the username “Altoid”, cross-posts were found across the internet that would lead to Ulbricht’s identification. This simply goes to show that we should never underestimate the power of a good OSINT investigator with too much time on their hands because you never know exactly what they’ll find.
The Big Arrest
At this point, it’s fair to say that arresting an international drug lord whose business is conducted electronically would be quite the battle and comes with complications that wouldn’t usually be present in other investigations. This problem was actually quite unique, as investigators realised that to achieve successful prosecution they’d need Ulbricht’s laptop. However, due to encryption, they’d need to catch it with the lid open and the power on, before copying essential files and configuring it so that it could be reaccessed later on.
The big day would come on the 1st of October in 2013, and it would be the FBI that would deal with the takedown.
Agents coordinating the arrest realised that the laptop provided a significant issue that could make or break the whole process and as such, the successful seizure of that laptop became the focus of the investigation. And to do it properly they would rely on something that would make anybody awkward in public — a fighting couple.
While we won’t bore you with the finer details of the arrest, what we can say is that FBI agents set up this “dispute” and in the midst of it the fighting lovers, would seize the laptop while other agents focused on controlling Ulbricht. The best bit though, was that this entire scene was set in a public library of all places!
The setup went off without a hitch, and investigators were able to arrest Ulbricht and successfully seize the laptop leading to a fresh trove of data that was used to fill in the blanks. Obviously, as an international drug lord, Ulbricht was not given bail. While most of 2014 would be taken up by the legal process and completion of the investigation, by the time mid-2015 rolled around Ulbricht was serving a double life sentence in a supermax prison.
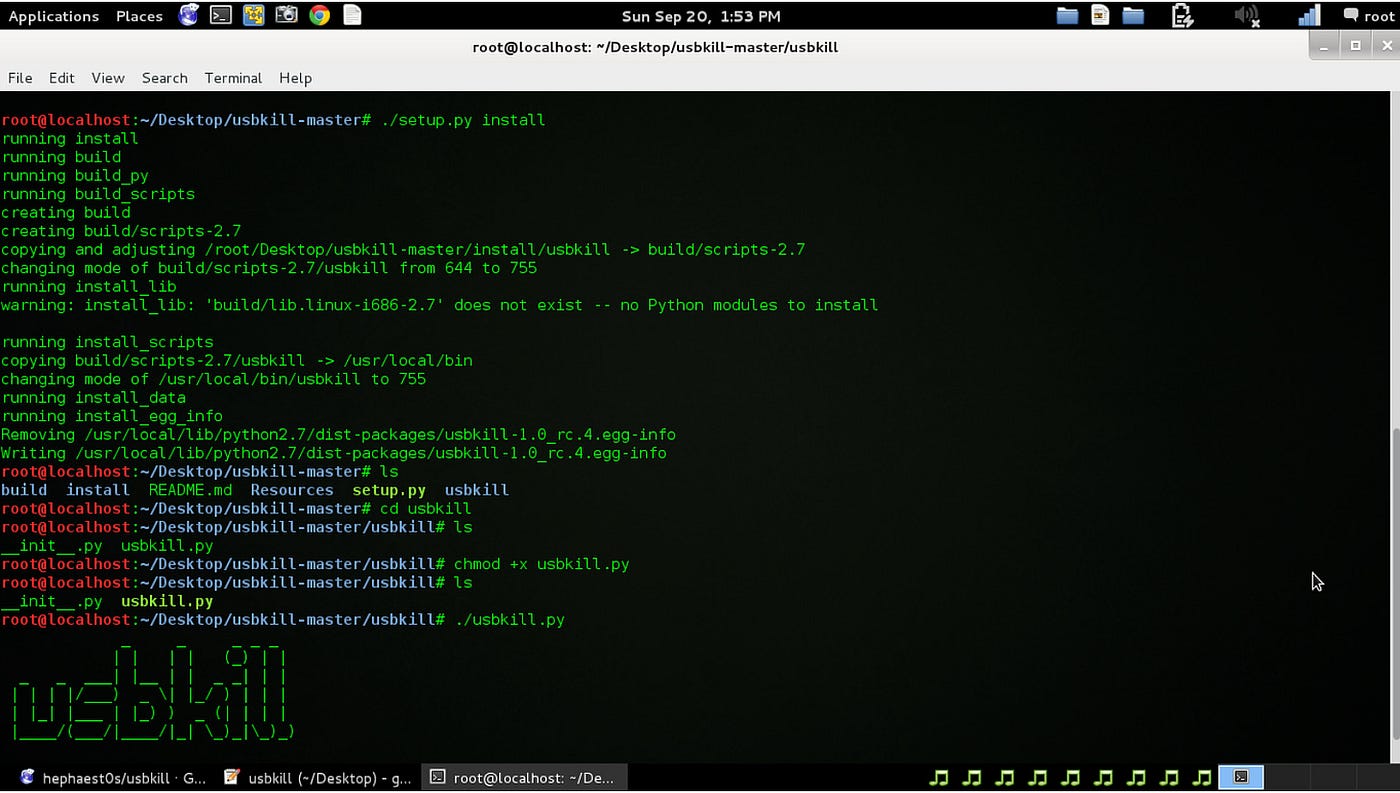
The last twist to this story is that some people were so incensed by Ulbricht’s arrest and the seizure of his laptop that they wrote code and programs attempting to mitigate this. USBKill provided mitigation strategies for those who were willing, and interestingly enough the arrest of Ulbricht is clearly listed as the motivator for writing this program.
The program provides a white list of USB devices and any device that isn’t on this whitelist and is installed leads to…..consequences for that machine. Nice. The GitHub repository for this code can be found here.
 Life Goes On
Life Goes On
You’d expect that taking out a place like Silk Road would lead to changes or at least delays for those who were involved but like many other things, life finds a way. And the Silk Road had barely been taken out before Alpha Bay launched, attempting to fill that spot in the market.
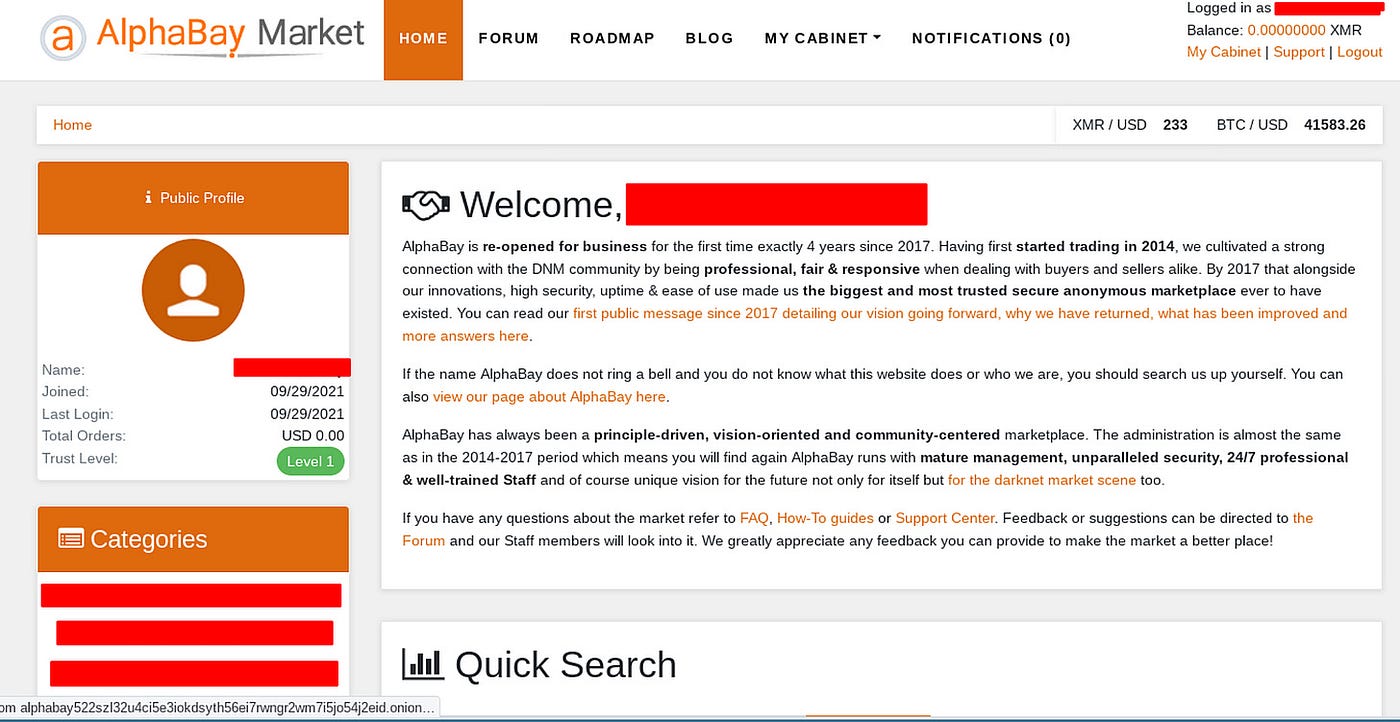
While the history of Alphabay is outside the scope of a single article, it’s an interesting read on its own and one that we might look at writing up later on as well. However, Alphabay wasn’t the only game in town and eventually other competitors would also get in on the game. Interestingly enough, Alphabay went through the same closures, challenges and issues that the Silk Road faced in the early days.
We can take away a few things from this story though. Firstly, true anonymity is difficult to find. Secondly, encryption is useless if you bypass it for your adversary. And lastly, the IRS always finds a way.
Medium has recently made some algorithm changes to improve the discoverability of articles like this one. These changes are designed to ensure that high-quality content reaches a wider audience, and your engagement plays a crucial role in making that happen.
If you found this article insightful, informative, or entertaining, we kindly encourage you to show your support. Clapping for this article not only lets the author know that their work is appreciated but also helps boost its visibility to others who might benefit from it.
🌟 Enjoyed this article? Support our work and join the community! 🌟
💙 Support me on Ko-fi: Investigator515
📢 Join our OSINT Telegram channel for exclusive updates or
📢 Follow our crypto Telegram for the latest giveaways
🐦 Follow us on Twitter and
🟦 We’re now on Bluesky!
🔗 Articles we think you’ll like:
- Signals From Space: The International Space Station
- Ukraine OSINT: Strava Strikes Again
✉️ Want more content like this? Sign up for email updates