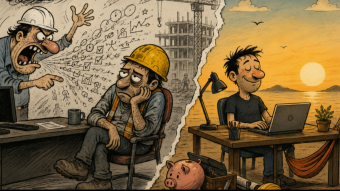
Cyberattacks are leaping ahead in sophistication and the industry is not prepared.
As an example, Google Project Zero team recently detected attackers that exploited a combination of seven previously unknown vulnerabilities (0-days) to hack fully patched Windows, Android, and IOS systems.
In this week’s video I cover the rapid advances of attackers, the strategic implications, and some areas in which the industry must adapt.
The cybersecurity industry must actively keep pace with the advancing capability of attackers.
Interested in more cybersecurity insights, rants, and strategic viewpoints?
- Subscribe to the Cybersecurity Insights channel on YouTube: https://www.youtube.com/c/CybersecurityInsights
Follow me on:
- LinkedIn: https://www.linkedin.com/today/author/matthewrosenquist
- Medium: https://medium.com/@matthew.rosenquist
- Twitter (@Matt_Rosenquist): https://twitter.com/Matt_Rosenquist