We received an email stating that our Trust Wallet update could not be completed due to some technical issue.
And unless we make a manual update, we will lose access to our assets.
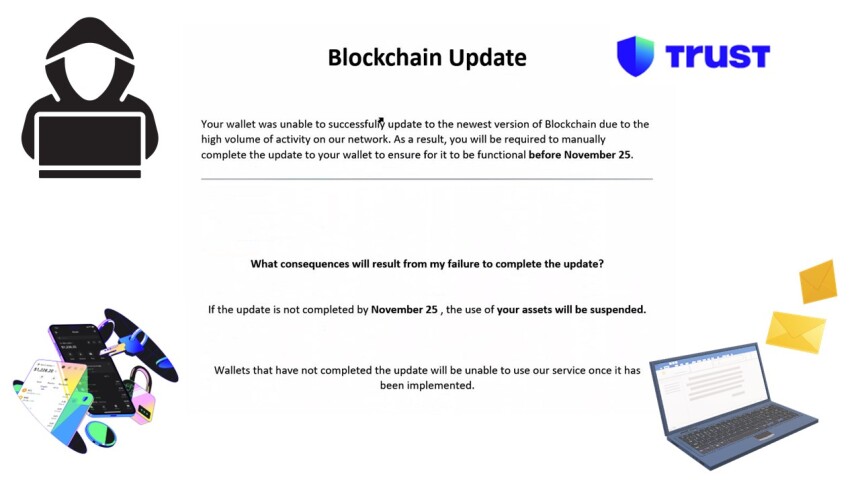
Thousands and thousands of very similar emails are being sent every single day.
While experienced crypto users will not fall for them, newcomers to the crypto space may actually fall victim to this scam because they have not been able to build sufficient awareness yet.
In this short 2-minute video we 'fall' for this scam and disclose our 12-word Trust Wallet seed phrase.
Why Do Scammers Use TinyURL
Before proceeding, we want to make it crystal clear that TinyURL is a legitimate service used by marketers and content creators.
But it can be also used by malicious people for malicious activities.
We do not blame Outlook or Gmail for being used by scammers to send phishing emails, because it is the scammer who is to be blamed.
TinyURL, the same as Outlook, Gmail, and many other legitimate services do take steps to prevent misuse of their service.
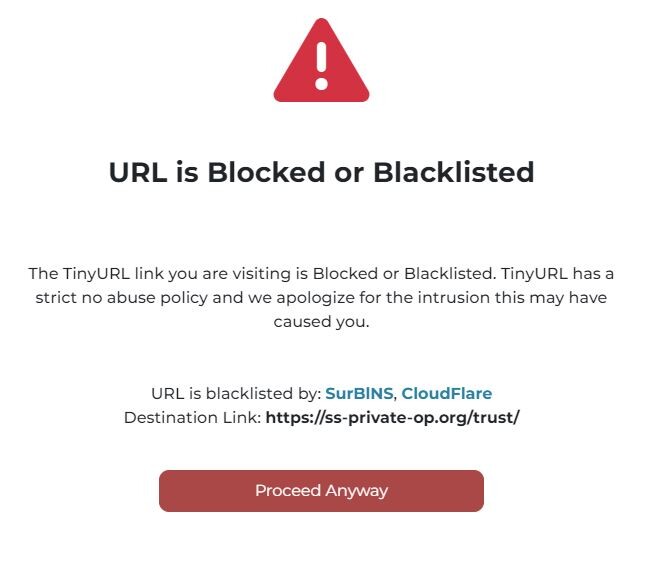
But, in any case, we must be aware of how scammers use URL shorteners for their own advantage:
Click Tracking: URL shortening services often provide analytics tools that allow users to track the number of clicks, the geographic location of users, and sometimes even the devices used to access the link.
This sort of data is very valuable for scammers because it can be used to assess the success of their phishing campaigns, gather information about the effectiveness of different lures, and refine their tactics.
Avoiding Blacklists: By using URL shorteners, scammers can potentially bypass email filters and security systems that might flag or block known malicious URLs.
Many security systems maintain lists of known malicious websites, and using a URL shortener can help scammers evade these blacklists temporarily. Rather than exposing their phishing website URL to be banned due to their emails being flagged as spam or phishing, they expose the shortened URL knowing that for them it is much easier and simpler to just create a new shortened URL pointing to the phishing website.
Easier Distribution: Shortened URLs are more convenient for scammers to distribute in phishing emails because they are less likely to trigger suspicion.
Longer or more complex URLs can look suspicious and be flagged by email filters as potential phishing attempts. Or, even the recipients of the emails can become suspicious if they spot a very long URL (see example in the section below)
URL Shorteners You Should Know About
TinyURL, while very popular, is not the only URL shortener used by scammers.
The same principle applies to the URL shorteners that we are going to mention below. These are tools that can be used for good or bad.
Bitly (bit.ly): Bitly is one of the most popular URL-shortening services. It provides link tracking and analytics, allowing scammers to monitor the success of their campaigns.
Bitly also offers custom short URLs, making it easier for scammers to create links that appear more legitimate.
Ow.ly: Ow.ly is a URL shortening service provided by Hootsuite, a social media management platform.
Ow.ly is designed to be used with Hootsuite's social media tools, but scammers may use it independently to shorten URLs and track clicks.
is.gd: is.gd is a simple URL shortening service that scammers might use due to its ease of use.
While it doesn't provide as many tracking features as some other services, is.gd can still be effective for creating short, clickable links.
Tiny.cc: Similar to TinyURL, Tiny.cc is another URL shortening service that allows scammers to create short links and track click-through statistics.
Tiny.cc is user-friendly and provides customization options for creating custom short URLs.
Rebrandly: Rebrandly is a URL-shortening service that allows users to create branded short links with custom domains.
Scammers may use Rebarandly to create links that appear more trustworthy by mimicking legitimate websites.
Dynamic Redirection as an Alternative to URL Shorteners
We are going to make a short reference to Dynamic Redirections to prevent the false understanding that only URL Shorteners are used in Physing emails.
In addition to URL Shorteners and Dynamic Redirection, there are other many techniques that hackers and scammers use in emails to take advantage of.
Dynamic Redirection involves the use of changing or dynamic URLs to redirect users through multiple stages before reaching the final destination, typically a phishing page.
Below there is an example of a phishing email that uses Dynamic Redirection.
Hoovering (WITHOUT clicking) over the 'Upgrade my wallet' button or over the 'View in web Browser' link, we can observe the target URL. You can try with any of your emails that contain a button or link. Just do NOT try with suspicious emails.
Hoover over a button or link and on the bottom left corner you should be able to spot and read the target URL.
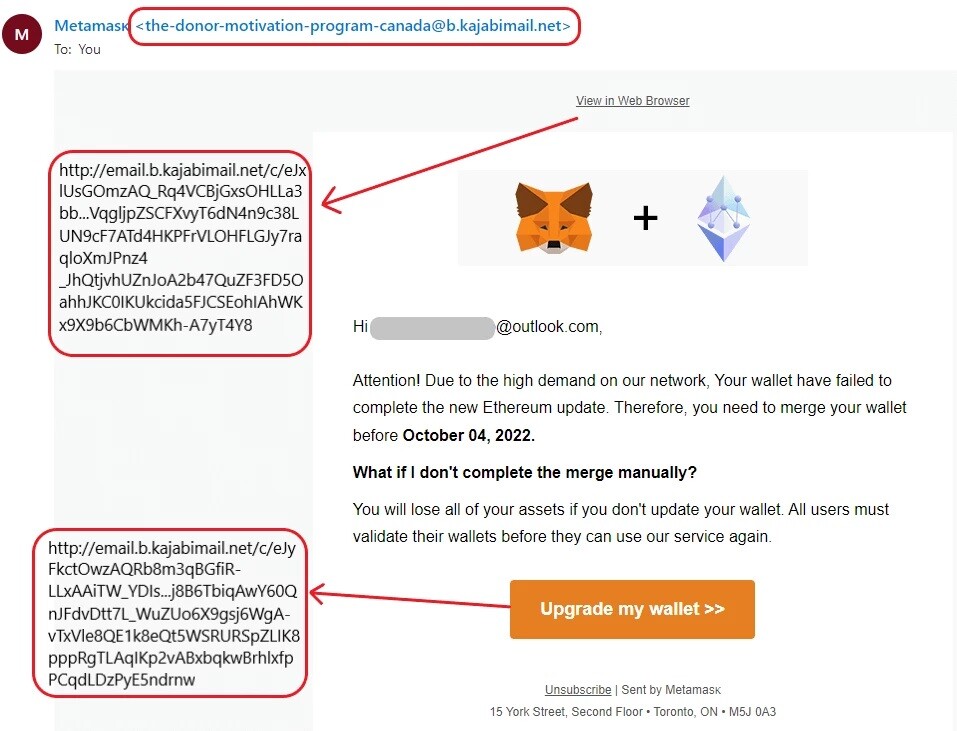
This technique, the Dynamic Redirection adds complexity to the attack and makes it more challenging for security systems to detect and block malicious content.
Here is a short description of how dynamic redirection can be used in phishing campaigns:
Initial Link in the Email: The phishing email contains an initial link, often disguised as a seemingly harmless button or clickable piece of text.
Redirection Stage: Clicking over the button or text, takes the victim-to-be to the first stage of redirection. It could be one or multiple stages. This stage, or stages, serve as a stepping stone to obfuscate the final destination.
The URLs involved in the redirection process may change dynamically over time. This means that even if security systems identify and block one set of URLs associated with the phishing campaign, the scammers can modify the redirection paths to avoid detection.
Final Phishing Page: After going through the various redirection stages, the victim-to-be finally lands on the phishing page.
This page is designed to mimic a legitimate login page, and it prompts the user to enter sensitive information such as usernames, passwords, or other personal details.
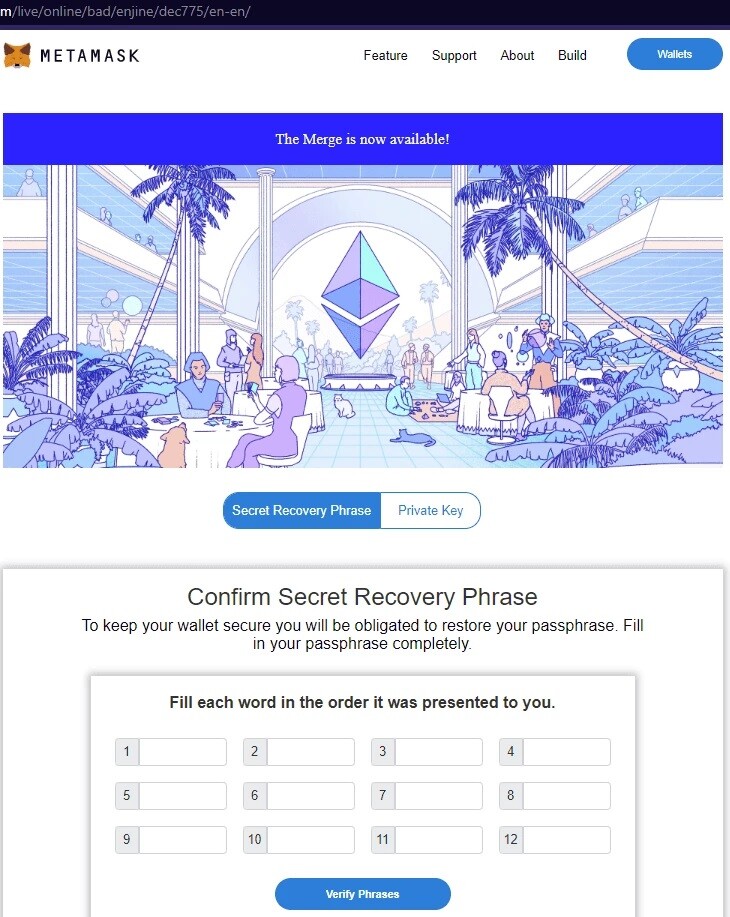
See the example below of a phishing website asking the victim to provide the Metamask wallet's Secret Recovery Phrase.
Unlikely the Trust wallet example, this time valid BIP-39 words are required from the victim. Most probably because the scammer wants to make sure that the victim does not make a mistake in this last phase of the scam, making the whole process useless to the scammer.
If this post has been of interest, you may be also interested in another Phishing Scam that we have recently reviewed: A Sensational Win: Mutant Ape NFT! (Phishing Scam Explored)

Congratulations on completing this 5-minute digital safety power-up.
We hope this short article has helped increase your digital safety knowledge and awareness, and the 5 minutes read was worth the time.
We will be exposing more scams so stay tuned if this topic does interest you.
For more 5-minute Power Power-Ups, please consider subscribing to our blog.









