In our time, everyone who uses computers or the internet needs passwords to access online accounts. Even access to devices, as well as virtual and
physical places may require passwords, PINs, or access codes. Some studies (see [1-4]) indicate that an average number of passwords a user needs to manage is above 100.
Any static password can be cracked with a brute force method with 100% of certainty. Indeed, basic parameters of static passwords are: a length of passwords (lp) and a length of a set of symbols (ls) from which passwords are constructed. From these two parameters we can calculate a number of all possible combinations (NAPC) of passwords with these parameters, which is equal to NAPC=ls^lp.
If a time for testing a single password is equal to t1, then the time t_crack=t1*NAPC is the time when the password's combination will be found with 100% certainty. It should be noted that with some luck, it is possible to find the correct combination even from a single attempt. The probability of such an event is small p=1/NAPC, but it is not zero.
Dynamic passwords are changeable static passwords. To understand how frequently passwords should be changed we need to understand two important definitions: an expected loss (EL) resulting from a compromised password and a level of tolerance (LT) to the loses resulting from a compromised password.
An expected loss (EL) due to a compromised password is equal to the product of the probability of the password being cracked and a real loss in the case of the password being cracked. For example, suppose that a real loss (RL) from the compromised password is one million dollars and the
probability that the password will be cracked in one day is equal to 0.00001. Then the expected loss for a day is equal to
EL(1 day)=$1,000,000*0.00001=10 dollars,
the expected loss for 10 days is equal to 100 dollars,
and the expected loss for 100 days is equal to 1,000 dollars.
A level of tolerance (LT) to the losses is the percentage of real loss you can tolerate. Once this parameter is determined, it is possible to calculate
a period for password changes from the equation: EL(T)=LT*RL.
For example, if the LT=0.1% then LT*RL=0.001*1,000,000 =1,000 dollars= EL(100 days).
Therefore, the passwords should be changed in 100 days to satisfy the level of tolerance LT=0.1%.
Dynamic passwords create inconveniences for users, because users need to securely manage these password changes. Online and offline password managers are proposed to address these inconveniences. But the big problem with these password managers is the problem of risk concentration. When users use such password managers, they put "all their eggs in one basket." The password managers store passwords in an encrypted file called a vault, which is a target for attackers. If attackers hack this vault, they will be able by using the brute force method to crack this vault at some point in time. Every year, researchers find weaknesses in such password managers (see [5-8]); therefore they are very risky for users.
A password management system, which allows one to generate multiple passwords for multiple sites or/and accounts in a simple way, which does not store passwords on computers or paper, which allows users to recreate/recover complex and strong passwords with easy memorable information, will be satisfactory for most users of passwords.
Many security experts will say: "Such system is not possible, because it is well known that there is a trade-off between security and convenience. If we want strong secure passwords then they must be complex and not memorable, which creates an inconvenience in use and management of these passwords. On the other hand, if we generate simple and memorable passwords, they will not be secure."
The password 123456 is easy to remember but is not secure. For many years this password was among the most popular.
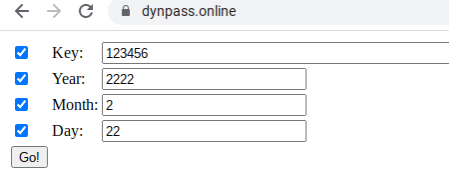
To convince skeptics, let us generate multiple strong passwords with a simple key: 123456 and the memorable date: February 22, 2222 with a public password generator (PG) available at URL https://dynpass.online . As we can see in the picture below, all fields on the form are hidden by default to prevent other people behind the user’s backs from seeing the entered data. Users should verify that no one can see the user’s input before entering data.
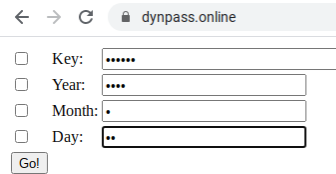
Fig. 1
By checking a checkbox near a field, we can make it visible.
Fig. 2
When we click on the "Go!" button, multiple passwords will be generated on the server and transferred via the secure internet communication protocol -HTTPS to the web browser on our computer. The passwords are not saved or stored on computers; they stay in the internal memory of the computer. The picture below shows the generated passwords.
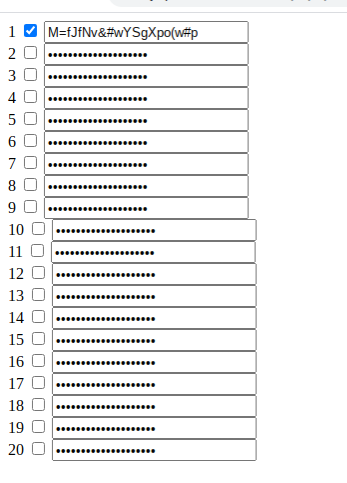
Fig. 3
As we can see in the picture, all fields on the form are hidden by default to prevent other people behind our backs from seeing the generated passwords. To see a particular password, we need to check the corresponding checkbox, after verifying that no one can see this password. The generated passwords are very secure as we can see from the picture below.
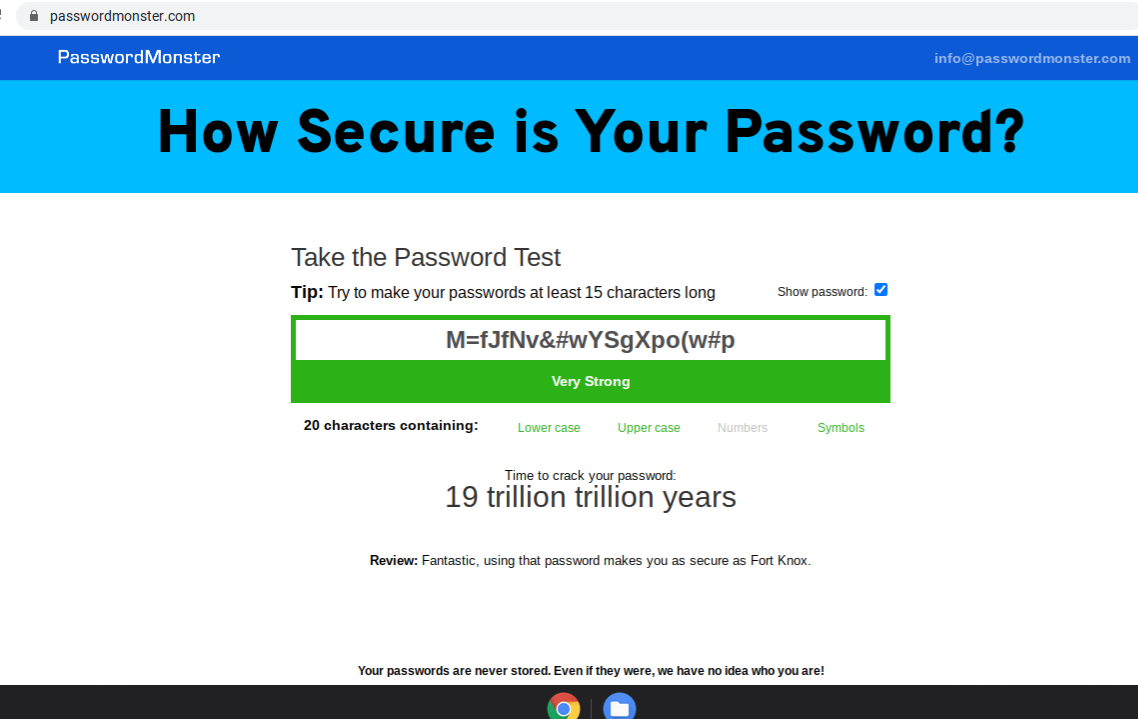
Fig. 4
For users, who prefer to work in a linux terminal, the script below will be helpful.
key='test'
day=2
month=2
year=2022
url='https://dynpass.online/dpt/dpt.php'
curl -X POST -F 'key='$key -F 'day='$day -F 'month='$month -F 'year='$year $url
The picture below shows the result of an execution of this script.

Fig. 5
Conclusions
1. With a single click of the button we generated multiple highly secure passwords for multiple sites/accounts, using the easily memorable key and date.
2. It is super easy to change these passwords on any given date, by changing the date and use the same key.
3. The generated passwords can not be hacked with traditional password hacking tools, because these passwords are not saved in an encrypted file. It is not possible to find a black cat in a black room, if there are no cats in this room.
In the next post we consider how to use this approach to solve crypto private keys -loss conundrum.
References [1] World Password Day: How to Improve Your Passwords https://blog.dashlane.com/world-password-day/#:~:text=According%20to%20our%202017%20findings,will%20skyrocket%20to%20300%20accounts [2] Study Reveals Average Person Has 100 Passwords https://tech.co/password-managers/how-many-passwords-average-person [3] Average person has 100 passwords - study https://securitybrief.co.nz/story/average-person-has-100-passwords-study [4] Struggling with password overload? You're not alone https://www.techradar.com/news/most-people-have-25-more-passwords-than-at-the-start-of-the-pandemic [5] Password Managers Have A Security Flaw -- Here's How To Avoid It https://www.forbes.com/sites/kateoflahertyuk/2019/02/20/password-managers-have-a-security-flaw-heres-how-to-avoid-it/?sh=656381704e16 [6] Password managers have a security flaw. But you should still use one. https://www.washingtonpost.com/technology/2019/02/19/password-managers-have-security-flaw-you-should-still-use-one/ [7] Which Password Managers Have Been Hacked? https://password-managers.bestreviews.net/faq/which-password-managers-have-been-hacked/ [8] Are password managers safe to use in 2021? https://cybernews.com/best-password-managers/are-password-managers-safe/



![[The $0 Growth Hack]: How To Build a 1-Million-User Empire in 2 months](https://cdn.publish0x.com/prod/fs/cachedimages/3731945950-e221973c3b382a1996b83b7ff6d063e191f6be57889a4e0bf3926d37de0a6d35.jpg)





