Linux has long been recognized as one of the most secure operating systems available on the market. Its reputation as a virtual fortress, resistant to cyber attacks, has captured the attention of technology experts and enthusiasts alike. What Makes Linux So Robust?
The Linux structure, based on an open source design, is a fundamental pillar of its security. Being publicly accessible, thousands of developers from around the world contribute to its constant improvement, identifying and correcting vulnerabilities quickly and effectively. This transparency fosters an active security community that collaborates to strengthen the system in real time.
Permission control in Linux is another crucial aspect that contributes to its unbreakability. Unlike other operating systems, Linux assigns different levels of access to users and processes, thus limiting the harmful potential of possible intrusions. This hierarchy of permissions prevents a malicious user from accessing sensitive areas of the system, dramatically reducing opportunities for exploitation.
The Strength of its Architecture. How does Linux Defend itself from Attacks? The Linux security model, based on the premise of "everything is a file", means that even hardware devices are represented as files in the file system. This abstraction provides an additional layer of security by allowing the kernel to manage system resources uniformly, without exposing them to external threats. Furthermore, regular updates are standard practice in the Linux world, and one of the main reasons behind its robustness. Security patches are deployed in a timely manner to address new vulnerabilities, thereby keeping the system protected against the latest cyber threats. This diligence in updating ensures that Linux is always one step ahead in the race against hackers.
The Linux security philosophy focuses on prevention rather than reaction. By implementing proactive measures such as enforcing access control policies and auditing logs, Linux positions itself as a bulwark against security breaches. This preventive mindset not only protects the system itself, but also promotes a culture of security awareness among its users. The diversity of Linux distributions is another factor that contributes to its reputation for invulnerability. With a wide range of options available, users can choose the distribution that best suits their security and privacy needs. This variety encourages innovation and competition, thus driving the continued evolution of the Linux ecosystem in terms of security.
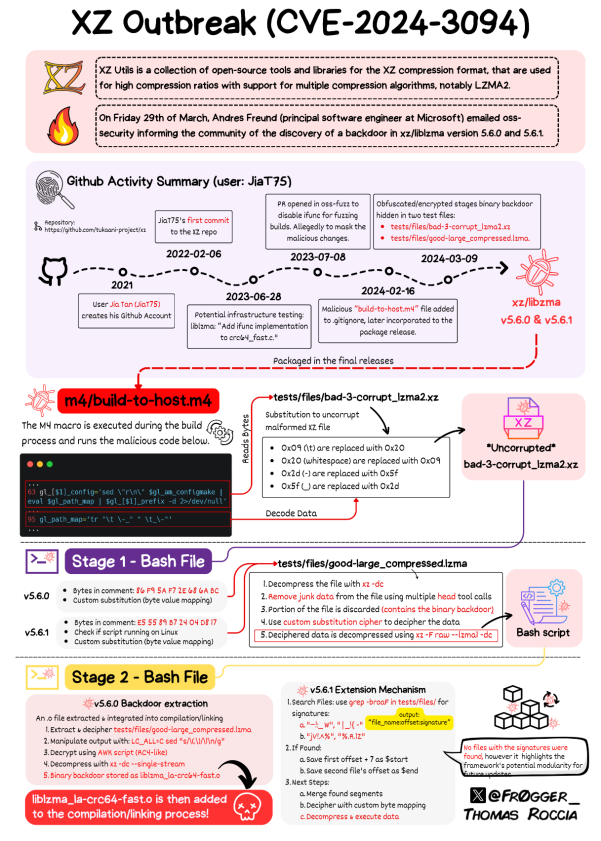
So far so good, however .............. however ........, in a twist worthy of a technological thriller, on Friday, March 29, an engineer from Microsoft stumbled upon one of the most sophisticated cyberattacks in Linux history. An attack so elaborate that it threatened to bring the entire world to its knees. And it is not an exaggeration.
Although as he explained, Linux is renowned for its robust security, the attackers did not target the core of the system. Instead, they opted for a cunning tactic known as "Supply Chain Attack". This involves violating components or libraries external to the kernel, but widely used within the system, which often lack the same levels of security.
A paradigmatic case of this strategy was the attack on specific libraries, such as the famous Heartbleed in 2014 and the more recent Log4Shell in 2022. In this scenario, the liblzma library, part of XZ Utils, was the entry point. XZ Utils, a file compression toolkit ubiquitous on Linux, Mac, and Windows, provided the perfect ground for infiltration.
But how did the attackers manage to infiltrate a seemingly unreachable target? The road to XZ Utils was filled with seemingly insurmountable obstacles. However, the perpetrators wove a master plot that unfolded over more than three years. The mastermind behind this operation, known as Jia Tan (or possibly a group with this pseudonym), set off a series of meticulously coordinated events. Starting in 2021, Jia Tan submitted a Pull Request to the libarchive project, quietly introducing unsafe code. This seemingly insignificant move laid the foundation for what was to come.
The Staging of the Attack. 2022 marked the beginning of the main phase of the attack. Jia Tan submitted a patch for XZ Utils, apparently benign. However, this act unleashed a series of carefully orchestrated pressures on Lasse Collin, the official maintainer of the project. In a series of exchanges on the XZ mailing list, the impeccable coordination between Jia Tan and other unknown actors is evident. From initial support to subtle pressure, each step was carefully planned to undermine trust in the maintainer and pave the way for infiltration.
The Linux hack episode, although terrifying, highlights the complexity and importance of supply chain security. From social engineering to meticulous coordination, the attackers demonstrated an unprecedented level of cunning. However, this incident also highlights resilience and collaboration in the tech community. With a deeper understanding of the risks and constant vigilance, we can strengthen our defenses against future attacks. Ultimately, this story serves as a reminder that cybersecurity is a constant battle, one in which we must all actively participate to protect our digital infrastructure.
⚠️ ALERT ⚠️ If you use versions 5.6.0 and 5.6.1 of liblzma on your team, you must update immediately, you can also check if your team is compromised in: https://xz.fail or with the protocol https://github.com/amlweems/xzbot
TOOLS, PLATFORMS & APPLICATIONS
💲 Tangled - 🎁 Pay me Internet 🎁. Generate passive income with a decentralized peer-to-peer ecosystem for consumers, advertisers, search, and social networks.
💲 Solcial - Social network on the Solana blockchain that allows users to share content without censorship or fear of prohibition and also earn money for their work. Users can also own their own content and tokens.
💲 Bulb, Publish0x - Earn cryptocurrencies, NFTs or money without investment.
💲 AddmeFast - Promote and increase the sources of traffic, visibility, reach and reputation of your social networks.
💲 BingX - Called "The People's Exchange", it places a strong emphasis on social trading and offers its clients extensive features.








![How Fear of Piracy [Destroyed] a 20-Year Tech Lead](https://cdn.publish0x.com/prod/fs/cachedimages/3731945950-5c99dbb082c081853735e98f1f9444ea30dc5a195fc83eee84721476c11215db.jpg)

