A Decentralized Approach to Cryptocurrency Custodianship
Custodians play a crucial role in the shielding mechanism that turns cryptocurrencies - like BTC, ETH and USDT - into privacy coins [Incognito, 2019a].
Existing custodian solutions like Bitgo and Coinbase Custody are centralized and expensive. Trusted third parties are security holes [Szabo, 2001]. In addition, the very nature of centralized custody necessitates the sharing of a user’s private information to third parties.
Incognito takes a decentralized approach to custodianship; there are multiple custodians instead of one centralized authority like Bitgo or Coinbase Custody. Anyone can become a custodian by simply supplying a bond.
A smart contract that controls bonds and runs exactly as programmed was implemented on Ethereum. Not only is the Bond smart contract trustless, it also provides real-time processing, as opposed to the multi-day manual process adopted by centralized custodian companies.
Initially, for simplicity’s sake, a fixed custodian fee structure was implemented. This could be further improved by implementing a market-driven custodian fee structure where users are able to set their own fees and custodians are able to compete for user deposits.
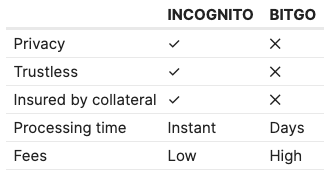
Table 1. A comparison between Incognito and centralized custodians like Bitgo and Coinbase Custody.
The Bond Smart Contract
The Bond smart contract glues together Incognito, custodians, and other cryptonetworks like Bitcoin and Binance Chain. There will be multiple implementations of the Bond smart contract on different cryptonetworks, including Incognito itself, using their respective cryptoassets as collateral.
The first implementation is programmed as an Ethereum smart contract [Wood, 2014]. Ethereum was chosen because its smart contract platform is battle-tested and it has many liquid cryptoassets that are suitable collateral types.
 Figure 1. The Bond smart contract is programmed to glue together custodians, Incognito, and other cryptonetworks like Bitcoin and Binance Chain.
Figure 1. The Bond smart contract is programmed to glue together custodians, Incognito, and other cryptonetworks like Bitcoin and Binance Chain.
The Bond smart contract is programmed to:
- Escrow collateral, in ETH and liquid ERC20 tokens, bonded by custodians
- Set the maximum total amount of user deposits that a custodian can accept based on the Collateral-to-Deposit ratio
- Verify deposit proofs on other cryptonetworks and submit valid proofs to Incognito for minting privacy coins
- Verify burn proofs of privacy coins on Incognito and instruct custodians to release public coins
- Verify custodians’ release proofs on other cryptonetworks and free up their collateral; custodians can withdraw their collateral tokens or take new user deposits
- Liquidate collateral when custodians misbehave or collateral amount drops below deposit amount
Over-Collateralized Bonds
Custodians must first bond some collateral into the Bond smart contract. Bonded collateral tokens are required as a recourse when custodians misbehave. The Bond smart contract only accepts ETH and liquid ERC20 tokens as collateral.
Because cryptocurrency prices are volatile, bond values are also volatile. It is necessary to ask custodians to overbond so that the total amount of user deposits to a single custodian does not exceed the total value of the collateral bonded by that custodian.
a parameter α was introduced and initially set as 150%. α is the Collateral-to-Deposit ratio, which makes sure that user deposits never exceed the amount of total custodian collateral even if there is a significant drop in collateral value.
For example, as a custodian, Alice needs to bond at least $1,500 worth of ETH and ERC20 tokens in the Bond smart contract if she wants to take $1,000 worth of BTC user deposits.
Auto-Liquidation
Over-collateralization ensures that custodians do not misbehave.
During the unshielding process, if Alice doesn’t send the public coins back to Bob in full, Alice’s bonded collateral will be used to repay Bob. In this case, the public coins that Bob receives – Alice’s collateral to be precise – may be different from Bob’s original public coin, but their total value is the same or greater than the value of Bob’s original deposit.
Auto-liquidation also kicks in if the value of bonded collateral drops significantly. Custodians must add more collateral to avoid auto-liquidation. A parameter 𝛽 was introduced and initially set as 110%. If α is the upper bound, 𝛽 is the lower bound or the liquidation threshold. 𝛽 is designed to make sure that total custodian collateral amounts do not drop below total user deposits.
A future improvement could be automatically liquidating collateral on a decentralized exchange like Kyber [Luu and Yaron, 2017], Uniswap [Adam, 2018], or Incognito pDEX [Incognito, 2019b].
Incentives
First, custodians earn shielding fees and unshielding fees. The initial fee structure is simple – a fixed shielding fee of 0.01% and an unshielding fee of 0.01%.
Later, as part of a market-driven pricing structure, users could set their own fees and custodians could choose to process the transactions with the highest fees first. A more complex fee structure would take into account shielding, unshielding, and custodial times.
Second, custodians also earn PRV, the native coin of Incognito, through shield mining. In traditional cryptonetworks, mining rewards come solely from block mining, where miners earn rewards for producing new blocks. In Incognito, there is shield mining in addition to block mining, where custodians also mine PRV for shielding public coins. The more a custodian shields, the bigger the PRV rewards the custodian earns. The Incognito DAO funds shield mining rewards.
The shield mining reward ri for a custodian ci at block height k, is computed as follows, where Rk is the total shield mining reward for that block, n is the number of custodians, and bi is the bonded collateral value from custodian ci .

Contents
-
Shielding Cryptocurrencies: Turning Any Cryptocurrency Into a Privacy Coin
-
Trustless Custodians: A Decentralized Approach to Cryptocurrency Custodianship
-
Sending Cryptocurrencies Confidentially: Ring Signature, Homomorphic Commitment, and Zero-Knowledge Range Proofs
-
Privacy at Scale with Sharding
-
Consensus: A Combination of PoS, pBFT, and BLS
-
Incognito Software Stack: Navigating the Incognito Source Code
-
Incognito Performance
-
Network Incentive: Privacy (PRV)
-
User-Created Privacy Coins
-
Use Cases: Privacy Stablecoins, Privacy DEX, Confidential Crypto Payroll, and more
-
Future Work: Smart Contracts, Confidential Assets, Confidential IP, and more
-
Conclusions, Acknowledgments, and References
* This article is published upon permission of Incognito team. I thank them for their permission.










